Troianul SharkBot Android fură criptomonede și atacă conturile bancare
Cleafy și ThreatFabric au descoperit un nou troian Android SharkBot care utilizează serviciul de accesibilitate pentru a fura acreditările din aplicațiile bancare și criptomonede din Italia, Regatul Unit și Statele Unite.
Potrivit experților, malware-ul s-a răspândit din octombrie 2021. Malware-ul nu a fost văzut în oficial Google Magazin Play încă; în schimb, operatorii săi par să păcălească utilizatorii să descarce și să instaleze manual aplicația pe dispozitivele lor (încărcare laterală). De exemplu, se ştie că SharkBot se poate deghiza în player media, aplicație de streaming, sau aplicații de recuperare a datelor.

După instalarea unei aplicații infectate cu SharkBot, malware-ul cere utilizatorului să-i acorde acces la serviciul de accesibilitate. Malware-ul folosește drepturile obținute pentru a simula atingerea ecranului și pentru a efectua diverse sarcini rău intenționate, inclusiv: acordându-și drepturi de administrator, afișarea ecranelor de conectare false, înregistrarea tastelor, interceptarea și ascunderea mesajelor SMS de autentificare cu doi factori, precum și accesarea aplicațiilor bancare și criptomonede în scopul transferului de fonduri.
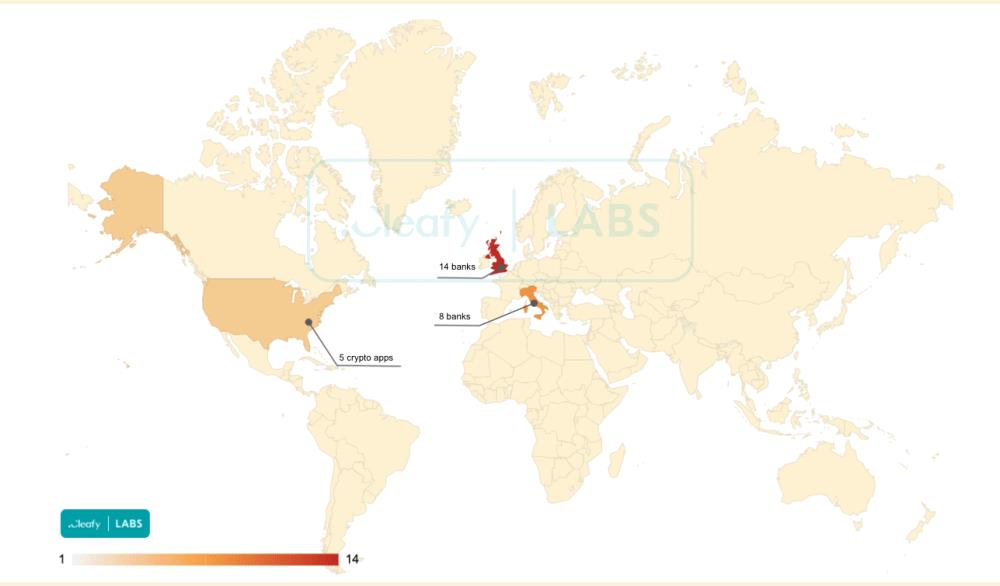
În prezent, SharkBot vizează 22 aplicații bancare care sunt utilizate în Italia și Marea Britanie, precum și cinci aplicații legate de criptomonede. În același timp, Experții în securitate cibernetică scriu că malware-ul este încă în stadiile incipiente de dezvoltare.

Permiteți-mi să vă reamintesc că și noi am scris asta Nou descoperit PhoneSpy Spyware-ul deja infectat 1000 Telefoane, şi că RezumatEmu Malware Android „rădăcinează” smartphone-urile și se sustrage de la detectare.




