A SharkBot Android trójai kriptovalutát lop, és bankszámlákat tör fel
Cleafy and ThreatFabric have discovered a new Android Trojan SharkBot that uses the Accessibility service to steal credentials from banking and cryptocurrency applications in Italy, az Egyesült Királyság és az Egyesült Államok.
According to experts, the malware has been spreading since October 2021. The malware has not been seen in the official Google Play Store yet; instead, its operators seem to trick users into downloading and manually installing the application on their devices (side-loading). Például, it is known that SharkBot can disguise itself as a media player, streaming application, or data recovery applications.

After installing an application infected with SharkBot, the malware asks the user to grant it access to the Accessibility service. The malware uses the obtained rights to simulate screen touches and perform various malicious tasks, including: granting itself administrator rights, displaying fake login screens, keylogging, intercepting and hiding two-factor authentication SMS messages, as well as accessing banking and cryptocurrency applications for the purpose of transferring funds.
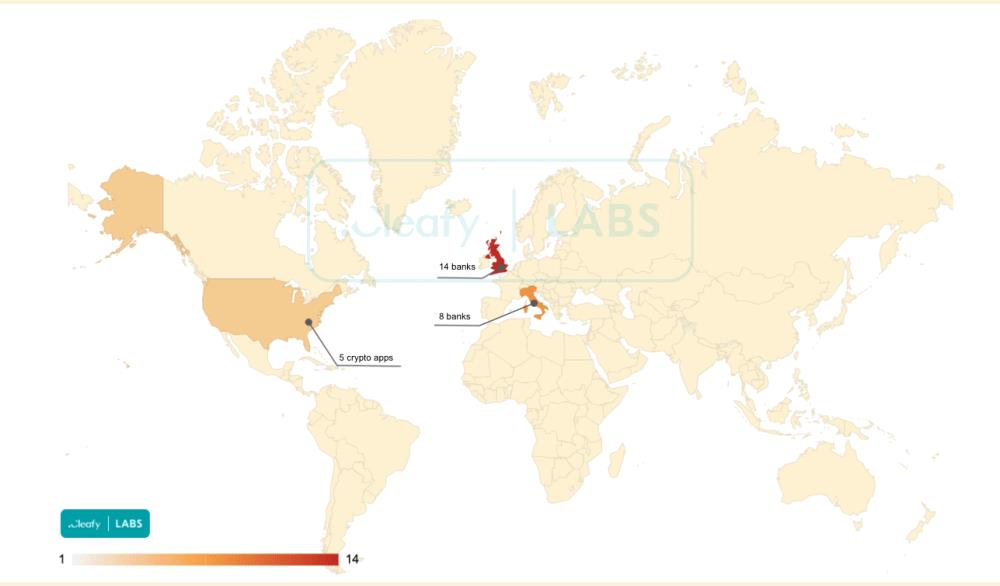
SharkBot is currently targeting 22 banking applications that are used in Italy and the UK, as well as five cryptocurrency related applications. Egy időben, cybersecurity experts write that the malware is still in the early stages of development.

Hadd emlékeztesselek, mi is ezt írtuk Újonnan felfedezett PhoneSpy A kémprogramok már fertőzöttek 1000 Telefonok, és az AbsztraktEmu Az Android rosszindulatú programjai „gyökerezik” az okostelefonokat, és elkerülik az észlelést.




