SharkBot Android tróverji stelur dulritunargjaldeyri og reiðhestur bankareikninga
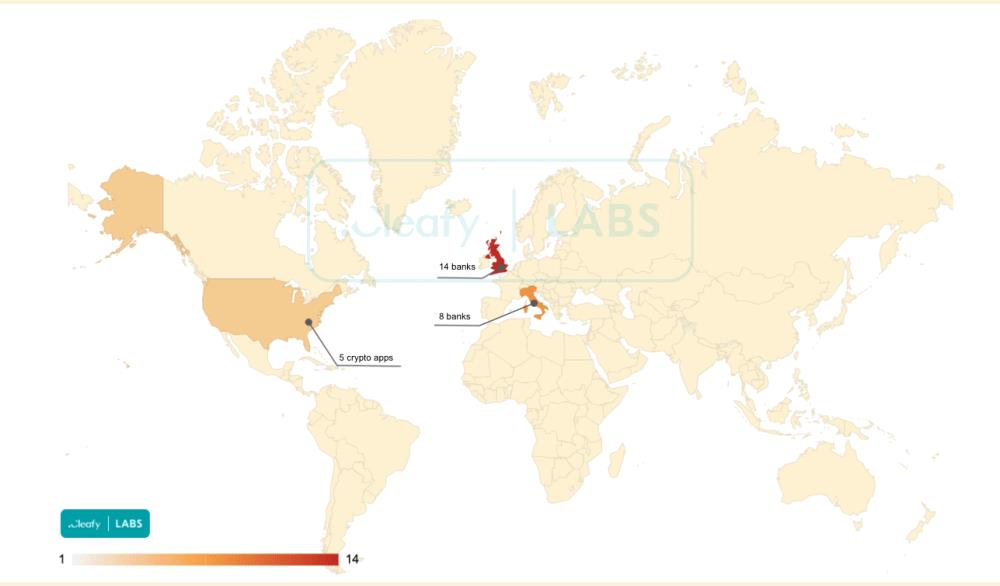
Cleafy og ThreatFabric hafa uppgötvað nýtt Android Trójuverji SharkBot sem notar aðgengisþjónustuna til að stela skilríkjum frá banka- og dulritunargjaldmiðlaforritum á Ítalíu, Bretlandi og Bandaríkjunum.
Samkvæmt sérfræðingum, spilliforritið hefur breiðst út síðan í október 2021. Spilliforritið hefur ekki sést í opinbera Google Play Store enn; í staðinn, Rekstraraðilar þess virðast plata notendur til að hlaða niður og setja upp forritið handvirkt á tæki þeirra (hliðarhleðsla). Til dæmis, það er vitað að SharkBot getur dulbúið sig sem fjölmiðlaspilara, streymisforrit, eða forrit til að endurheimta gögn.

Eftir að hafa sett upp forrit sem er sýkt af SharkBot, spilliforritið biður notandann um að veita honum aðgang að aðgengisþjónustunni. Spilliforritið notar tiltekinn rétt til að líkja eftir snertingu á skjánum og framkvæma ýmis skaðleg verkefni, þar á meðal: veitir sjálfum sér stjórnendaréttindi, sýna falsa innskráningarskjái, keylogging, stöðva og fela tveggja þátta auðkenningar SMS skilaboð, auk aðgangs að banka- og dulritunarforritum í þeim tilgangi að millifæra fjármuni.
SharkBot er núna að miða 22 bankaforrit sem eru notuð á Ítalíu og Bretlandi, auk fimm forrita sem tengjast dulritunargjaldmiðli. Á sama tíma, Sérfræðingar í netöryggi skrifa að spilliforritið sé enn á frumstigi þróunar.

Ég minni á að við skrifuðum það líka Nýlega uppgötvað PhoneSpy Njósnaforrit þegar sýkt yfir 1000 Símar, og það ÁgripEmu Android spilliforrit „rótar“ snjallsímum og forðast uppgötvun.




