Newly discovered PhoneSpy Spyware Already Infected Over 1000 Phones
More than 1,000 Android devices have been infected with the new PhoneSpy spyware, which secretly records audio and video in real time, steals files and performs many other spyware actions, according to Zimperium. The malware is primarily targeted at South Korean users.
In total, the researchers found 23 apps that secretly installed spyware on users’ devices. Among them were Yoga companion app, Kakao Talk messenger, image gallery browser, photo editing tool and more.
During installation, such applications ask the victim to grant numerous permissions, but this is the only thing that can raise suspicion from the user – otherwise, PhoneSpy behaves stealthily.
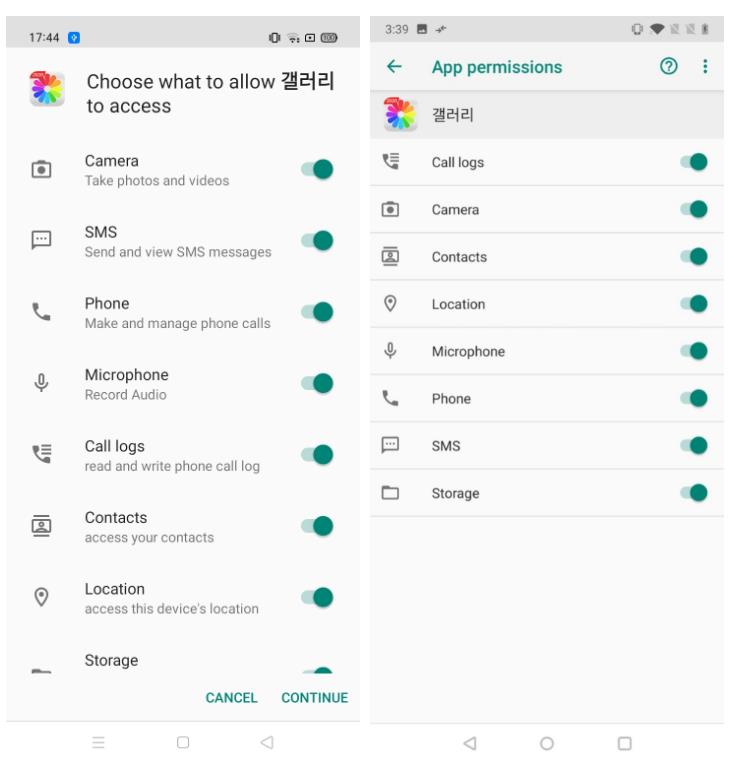
Malware asks for permissions
Zimperium experts did not find any evidence that infected applications are available on Google Play or other app stores. Therefore, they suspect PhoneSpy is spreading through traffic redirection or social engineering.
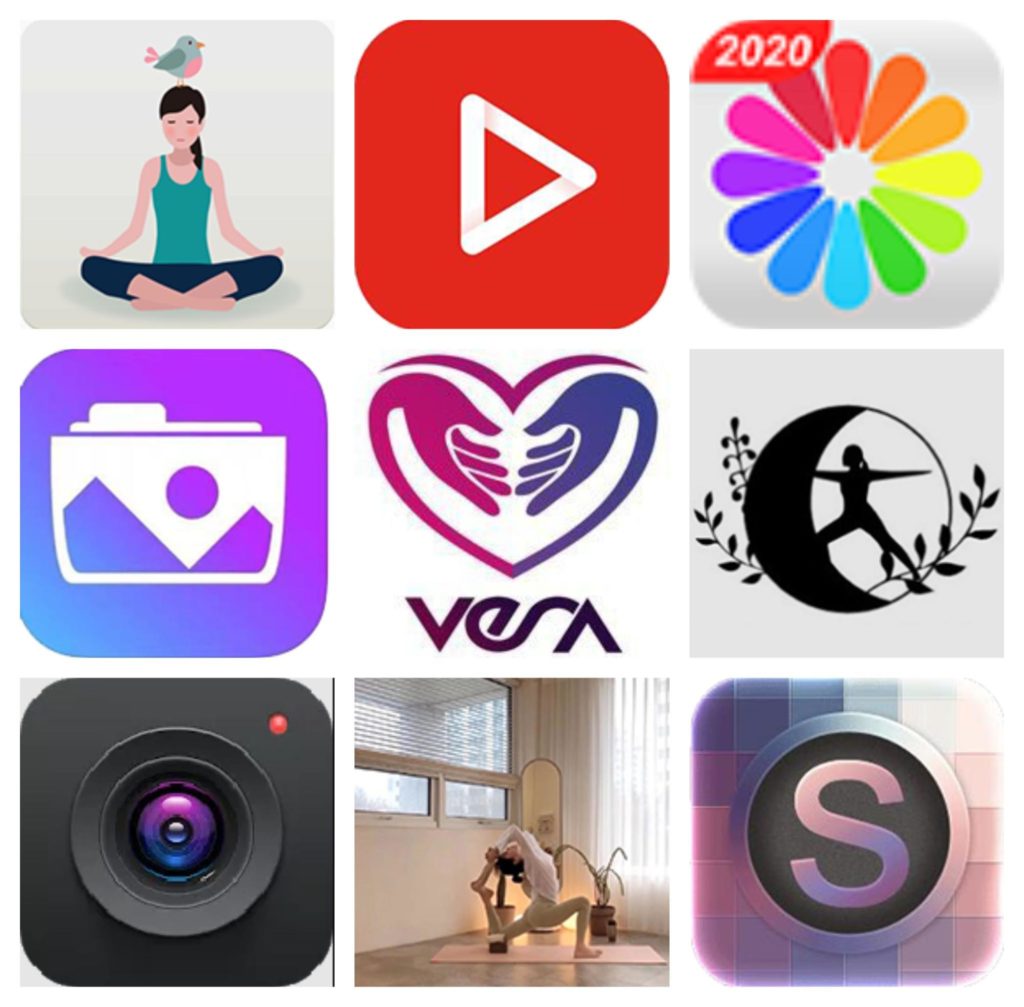
Infected applications
The spyware built into such applications and offers a wide range of features and spy functions. In essence, PhoneSpy works like a Remote Access Trojan (RAT) that receives and executes commands from its operators to collect and steal data and more. So, PhoneSpy can:
- collect a complete list of installed applications;
- steal credentials using phishing (the malware has templates for Facebook, Instagram, Kakao, and Google);
- steal images;
- track locations via GPS;
- steal SMS messages;
- steal phone contacts;
- steal call logs;
- record audio in real time;
- record video in real time using the front and rear cameras of the device;
- access the camera to take photos with the front and rear cameras;
- send SMS to a phone number controlled by the attacker with a text controlled by the attacker;
- retrieve information about the device (IMEI, brand, device name, Android version);
- hide your presence in the system by hiding your icon.
Let me remind you that we also wrote that Windows exploits and DevilsEye spyware are associated with the Israeli company Candiru.




