研究人員發現了針對 Windows Server 容器和 Kubernetes 集群的 Siloscape 惡意軟件
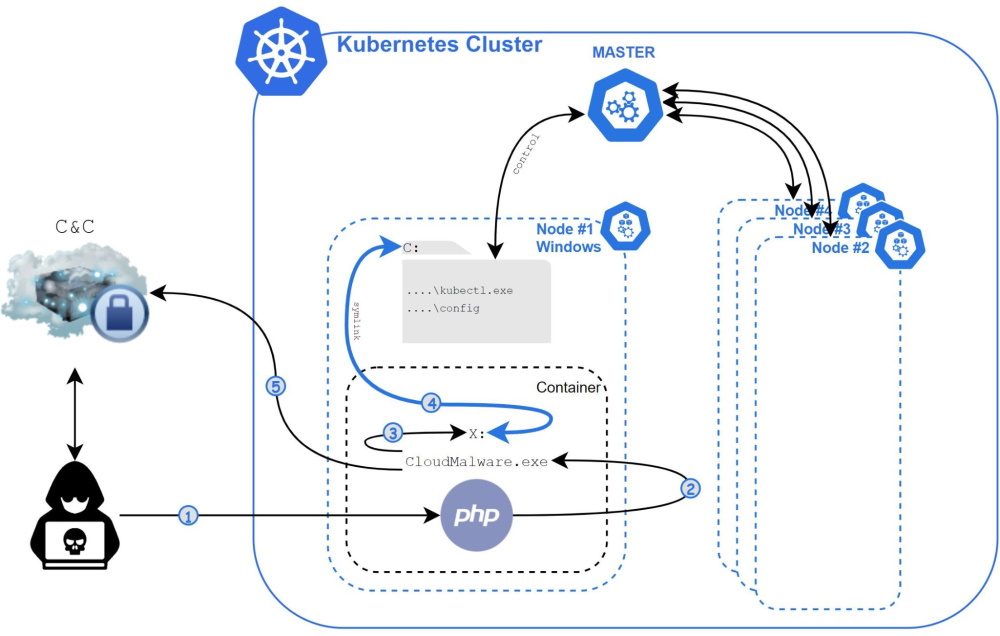
帕洛阿爾托網絡的研究人員 發現了 高度混淆的Siloscape惡意軟件,可損壞Windows Server容器以妥協Kubernetes簇. 攻擊者的最終目標是部署可用於其他惡意活動的後門.
專家寫道,三月初首次注意到這種攻擊, 但是他們已經持續了至少一年. 該廣告系列背後的攻擊者掃描網絡以獲取通用雲應用程序,然後將其用於各種舊漏洞.
如果網絡應用程序在Windows Server容器中運行, 攻擊者使用Siloscape惡意軟件, 利用先前記錄的逃生容器方法以訪問基礎操作系統.
如果操作系統作為kubernetes節點運行, 黑客還提取節點的憑據,然後使用它們導航到Kubernetes後端基礎架構並部署具有惡意功能的新節點.
黑客入侵整個集群比損害單個容器要嚴重得多, 由於集群可以運行多個雲應用程序, 而單個容器通常運行一個雲應用程序. 例如, 攻擊者可以竊取敏感信息,例如用戶名和密碼, 機密和內部組織文件, 甚至託管在集群上的整個數據庫.帕洛阿爾托網絡專家說
Siloscape還下載並在受感染系統上安裝TOR客戶端以與其C通信&C服務器並通過IRC從其運營商接收命令.
Palo Alto Networks公司專家報告說,他們能夠訪問該服務器, 目前攻擊者感染了超過 300 系統. 同時, 黑客的最終目標並不完全清楚.
“與其他針對容器的惡意軟件不同,主要針對加密夾, Siloscape實際上並沒有採取任何措施來損害簇本身. 代替, 它重點是確保無法檢測和跟踪, 並將後門打開到集群中,”專家說.
據推測,攻擊者可以向其他罪犯出租,訪問一些大型妥協的公司, 包括勒索軟件運營商.
據研究人員稱, 公司應盡快開始將應用程序從Windows容器移動到Microsoft Hyper-V, 正如微軟本身建議使用Microsoft Hyper-V,而不是舊且較不安全的容器機制.
Siloscape顯示了容器安全的重要性, 因為惡意軟件將無法造成任何重大損害,如果沒有容器逃脫. 至關重要的是,組織保持良好配置和安全的雲環境以防止此類威脅.
讓我提醒你,我也談到了這樣一個事實 XCSSET 惡意軟件在 macOS 中使用 0-day 攻擊.




