Researchers discovered Siloscape malware targeting Windows Server containers and Kubernetes clusters
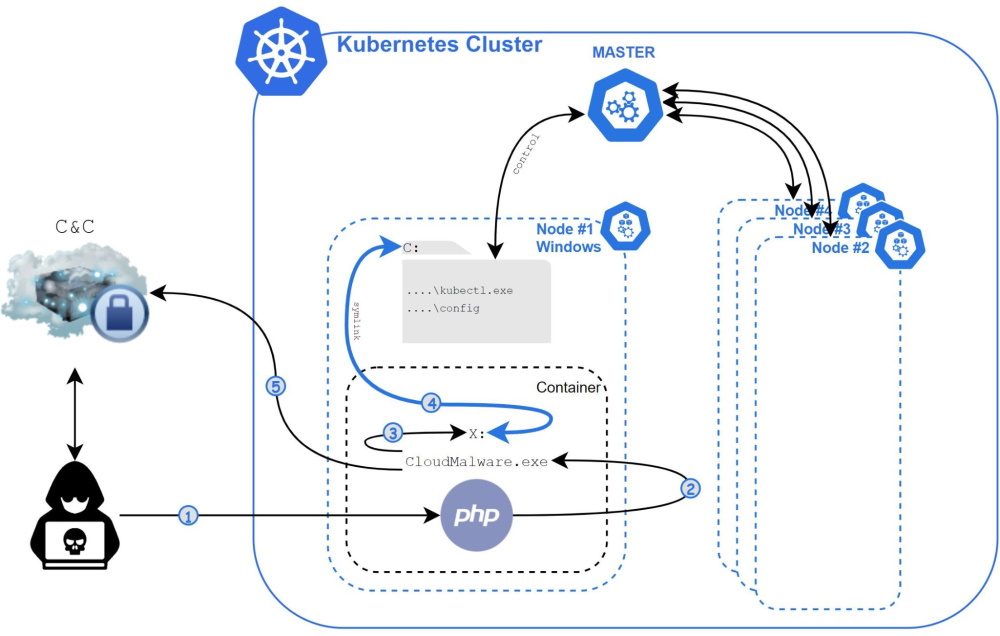
Researchers at Palo Alto Networks have discovered a highly obfuscated Siloscape malware that breaks into Windows Server containers in order to compromise Kubernetes clusters. The ultimate goal of attackers is to deploy a backdoor that can be used for other malicious activities.
Experts write that for the first time such attacks were noticed in early March, but they have been going on for at least a year. The attackers behind this campaign scan the network for common cloud applications and then use exploits against them for various old vulnerabilities.
If a web application is running inside a Windows Server container, attackers use the Siloscape malware, which exploits the previously documented escape container method to gain access to the underlying OS.
If the OS is running as a Kubernetes node, hackers also extract the node’s credentials and then use them to navigate to the Kubernetes back-end infrastructure and deploy new nodes with malicious features.
Siloscape also downloads and installs a Tor client on the infected system to communicate with its C&C server and receive commands from its operators via IRC.
Palo Alto Networks company specialists report that they was able to gain access to this server, and currently attackers have infected more than 300 systems. At the same time, the ultimate goal of the hackers is not completely clear.
“Unlike other malware targeting containers and mainly targeting cryptojacking, Siloscape doesn’t actually do anything to damage the cluster itself. Instead, it focuses on ensuring that it cannot be detected and tracked, and opens a backdoor into the cluster,” the experts say.
It is speculated that attackers could lease to other criminals access to some of the larger compromised companies, including the ransomware operators.
According to the researchers, companies should start moving applications from Windows containers to Microsoft Hyper-V as soon as possible, as Microsoft itself recommends using Microsoft Hyper-V instead of the old and less secure container mechanism.
Siloscape shows the importance of container security, as the malware wouldn’t be able to cause any significant damage if not for the container escape. It is critical that organizations keep a well-configured and secured cloud environment to protect against such threats.
Let me remind you that I also talked about the fact that XCSSET malware uses 0-day attacks in macOS.




