研究人員將 TrickBot 開發人員與 Diavol 勒索軟件聯繫起來
Fortinet專家出版了 報告, 他們認為著名惡意軟件trick腳的創造者 (這個黑客組通常稱為嚮導蜘蛛) 可能參與了新的Diavol勒索軟件的開發.
6月初,在各種系統上部署了勒索軟件的有效載荷 2021. 注意到這些勒索軟件非常相似,有很多共同點, 通過在文件加密期間使用異步I/O操作, 對相同的函數使用幾乎相同的命令行參數 (例如, 創建日誌, 加密磁盤和網絡資源, 掃描網絡).
然而, 專家仍然找不到Diavol勒索軟件與Trickbot的作者之間的直接聯繫, 而且, 他們發現了一些重要的差異. 例如, Diavol沒有內置的檢查,可以防止有效載荷在俄羅斯和順式國家 /地區的系統上觸發. 也, 新惡意軟件在加密之前不會竊取數據.
同時, 前幾天,Kryptos Logic宣布 它發現了變化 在Trickbot惡意軟件本身的代碼中. 據專家介紹, 自六月以來 2021, Trickbot一直在感染的機器上啟動一個新的模塊,該機器包含舊銀行組件的更新版本,該版本試圖竊取電子銀行登錄憑據.
此組件已重寫,現在包括將惡意代碼注入銀行網站的新方法. 專家建議將新代碼從舊的宙斯銀行家複製: 注射通過通過本地襪子服務器代理流量來工作. 如果流量中遇到在線銀行登錄頁面, 經過修改以竊取憑據或執行其他惡意動作. 假設以這種方式,Trickbot的開發人員正在嘗試與其他銀行木馬競爭並吸引他們的一些客戶.
Trickbot是迄今為止最大,最成功的惡意軟件威脅之一. 惡意軟件首先被發現回到 2015, 一系列備受矚目的逮捕後不久,這顯著改變了Dyre Hack群的組成.
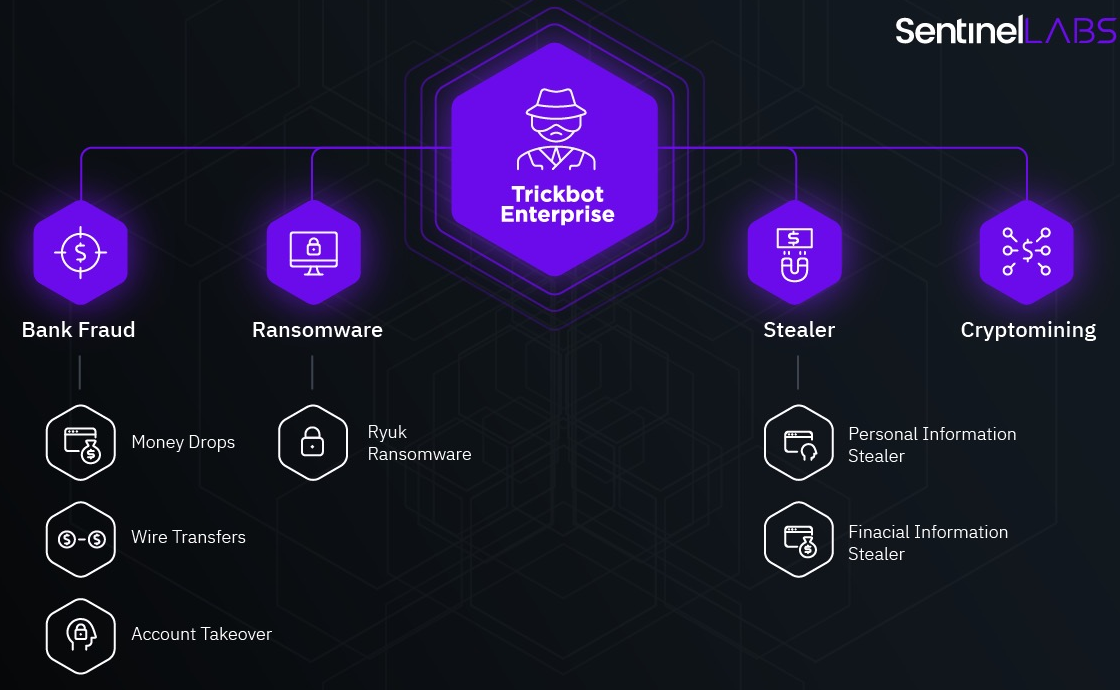
這些年來, 惡意軟件已經從旨在從銀行帳戶中竊取資金的經典銀行特洛伊木馬演變為散佈其他威脅的多功能滴管 (從礦工到勒索軟件和信息竊取者).
在秋天 2020, 一個 大規模操作 是為了消除Trickbot而進行的. 執法機構參加了, Microsoft Defender團隊的專家, 非營利組織FS-ISAC, 以及埃塞特, 流明, NTT和Symantec.
當時, 許多專家 財富網 儘管微軟能夠禁用Trickbot基礎架構, 殭屍網絡最有可能 “存活” 最終,其運營商將運行新的控制服務器並繼續其活動. 不幸, 這正是發生的事情.
讓我提醒你,我也談到了這樣一個事實 MountLocker勒索軟件使用Windows API導航網絡.




