Forscher haben TrickBot-Entwickler mit Diavol-Ransomware in Verbindung gebracht
Fortinet specialists published a Prüfbericht, in which they argue that the creators of the well-known malware TrickBot (this hack group is usually called the Wizard Spider) may be involved in the development of a new Diavol ransomware.
Payloads of ransomware Diavol and Conti were deployed on various systems in early June 2021. It is noted that these ransomware are very similar and have a lot in common, from using asynchronous I/O operations during file encryption, fast identische Befehlszeilenparameter für dieselben Funktionen zu verwenden (beispielsweise, Protokolle erstellen, Verschlüsselung von Festplatten und Netzwerkressourcen, scanning a network).
jedoch, experts still could not find a direct connection between the Diavol ransomware and the authors of TrickBot, moreover, Sie fanden eine Reihe wichtiger Unterschiede. Zum Beispiel, Diavol does not have built-in checks that prevent payload from being triggered on systems in Russia and CIS countries. Ebenfalls, the new malware does not steal data before encryption.
inzwischen, the other day Kryptos Logic announced that it had found changes in the code of the TrickBot malware itself. Nach Meinung von Experten, since June 2021, TrickBot has been launching a new module on infected machines containing an updated version of the old banking component that tries to steal e-banking login credentials.
This component has been rewritten and now includes new methods for injecting malicious code into bank websites. Experts suggest that the new code is copied from the old Zeus banker: injections work by proxying traffic through a local SOCKS server. If online banking login pages are encountered in traffic, the traffic is modified to steal credentials or perform other malicious actions. It is assumed that in this way the developers of TrickBot are trying to compete with other banking Trojans and entice some of their customers.
TrickBot is one of the largest and most successful malware threats to date. Malware was first spotted back in 2015, shortly after a series of high-profile arrests that significantly changed the composition of the Dyre hack group.
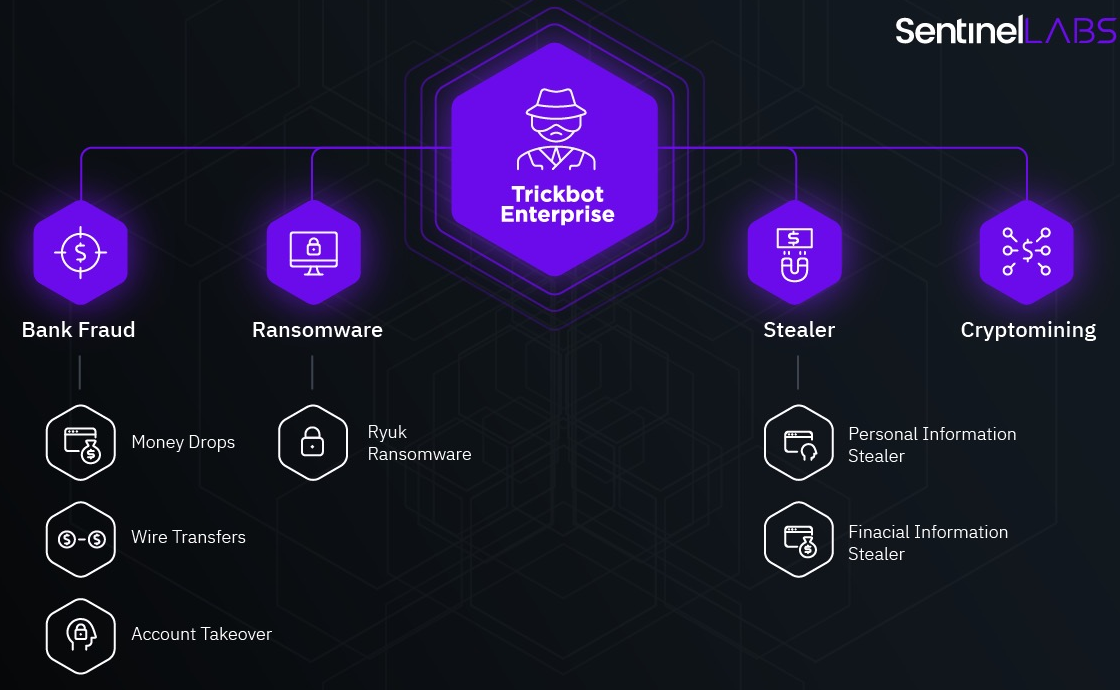
Über die Jahre, malware has evolved from a classic banking Trojan designed to steal funds from bank accounts to a multifunctional dropper that spreads other threats (from miners to ransomware and info-stealers).
In the fall of 2020, ein large-scale operation was carried out aimed at eliminating TrickBot. It was attended by law enforcement agencies, specialists from the Microsoft Defender team, the non-profit organization FS-ISAC, as well as ESET, Lumen, NTT and Symantec.
At that time, many experts Fortinet that although Microsoft was able to disable the TrickBot infrastructure, most likely the botnet will “survive” and eventually its operators will put into operation new control servers and continue their activity. Unglücklicherweise, this is exactly what happened.
Lassen Sie mich daran erinnern, dass ich auch darüber gesprochen habe, dass Die MountLocker-Ransomware verwendet die Windows-API, um im Netzwerk zu navigieren.




