Forskere forbandt TrickBot-udviklere med Diavol ransomware
Fortinet-specialister udgav en rapport, hvor de hævder, at skaberne af den velkendte malware TrickBot (denne hackgruppe kaldes normalt for Wizard Spider) kan være involveret i udviklingen af en ny Diavol ransomware.
Nyttelaster af ransomware Diavol og Conti blev implementeret på forskellige systemer i begyndelsen af juni 2021. Det bemærkes, at disse ransomware er meget ens og har meget til fælles, fra at bruge asynkrone I/O-operationer under filkryptering, at bruge næsten identiske kommandolinjeparametre til de samme funktioner (for eksempel, oprettelse af logs, kryptering af diske og netværksressourcer, scanning af et netværk).
Imidlertid, eksperter kunne stadig ikke finde en direkte forbindelse mellem Diavol ransomware og forfatterne af TrickBot, desuden, de fandt en række vigtige forskelle. For eksempel, Diavol har ikke indbyggede checks, der forhindrer, at nyttelast udløses på systemer i Rusland og CIS-lande. Også, den nye malware stjæler ikke data før kryptering.
I mellemtiden, forleden annoncerede Kryptos Logic det den havde fundet ændringer i koden til selve TrickBot-malwaren. Ifølge eksperter, siden juni 2021, TrickBot har lanceret et nyt modul på inficerede maskiner, der indeholder en opdateret version af den gamle bankkomponent, der forsøger at stjæle e-bank login-legitimationsoplysninger.
This component has been rewritten and now includes new methods for injecting malicious code into bank websites. Eksperter foreslår, at den nye kode er kopieret fra den gamle Zeus-bankmand: indsprøjtninger virker ved at proxyisere trafik gennem en lokal SOCKS-server. Hvis du støder på login-sider til netbank i trafikken, the traffic is modified to steal credentials or perform other malicious actions. It is assumed that in this way the developers of TrickBot are trying to compete with other banking Trojans and entice some of their customers.
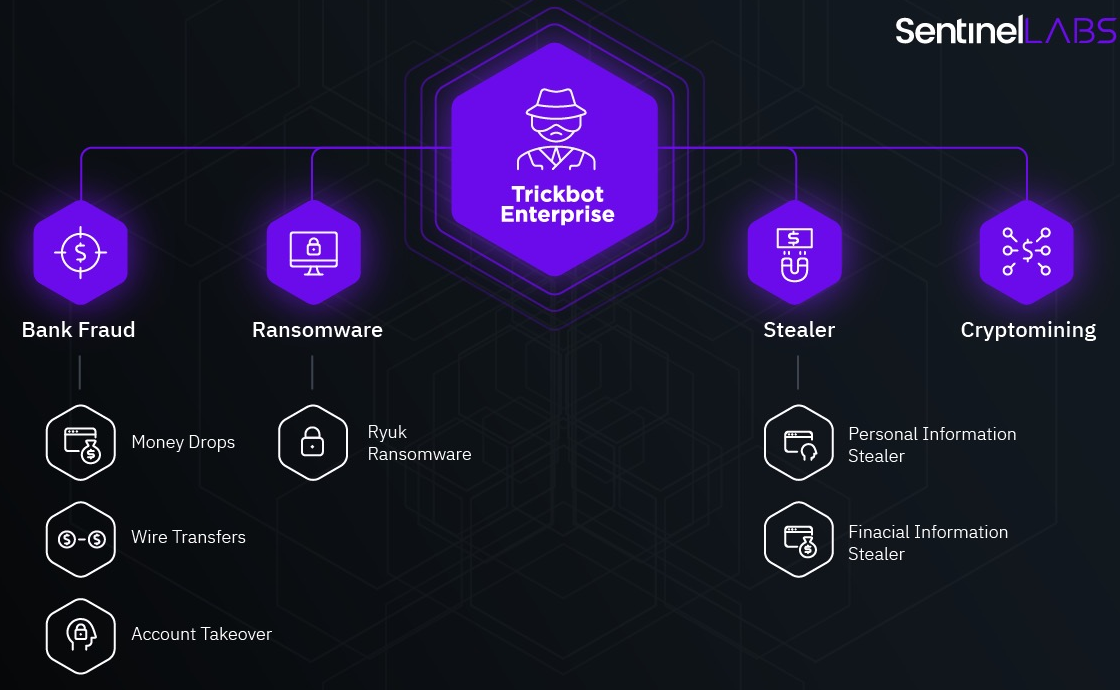
TrickBot is one of the largest and most successful malware threats to date. Malware blev først opdaget igen 2015, shortly after a series of high-profile arrests that significantly changed the composition of the Dyre hack group.
I årenes løb, malware har udviklet sig fra en klassisk banktrojaner designet til at stjæle penge fra bankkonti til en multifunktionel dropper, der spreder andre trusler (fra minearbejdere til ransomware og info-tyvere).
I efteråret 2020, -en storstilet drift blev udført med det formål at eliminere TrickBot. Det blev overværet af retshåndhævende myndigheder, specialister fra Microsoft Defender-teamet, non-profit organisationen FS-ISAC, samt ESET, Lumen, NTT og Symantec.
På det tidspunkt, mange eksperter De amerikanske og britiske regeringer det selvom Microsoft var i stand til at deaktivere TrickBot-infrastrukturen, højst sandsynligt vil botnettet “overleve” og til sidst vil dets operatører sætte nye kontrolservere i drift og fortsætte deres aktivitet. uheldigvis, det er præcis, hvad der skete.
Lad mig minde dig om, at jeg også talte om det faktum, at MountLocker ransomware bruger Windows API til at navigere på netværket.




