AbstractEmu Android malware “roots” smartphones and evades detection
Researchers at Lookout Threat Labs 發現 a new Android malware called AbstractEmu, which “roots” infected devices, which has become a rather rare practice for such malware in recent years.
AbstractEmu came bundled with 19 apps distributed through Google Play and third-party app stores (包括 Amazon Appstore, Samsung Galaxy Store, Aptoide, and APKPure).
The infected applications were password managers and various system tools, including tools for saving data and launching applications. 同時, in order to avoid suspicion, they all really worked and had the declared functionality.
The malicious apps have now been removed from the Google Play Store, but other app stores are probably still distributing them. Researchers say that only one of the infected applications, Lite Launcher, had over 10,000 downloads when it was removed from Google Play.
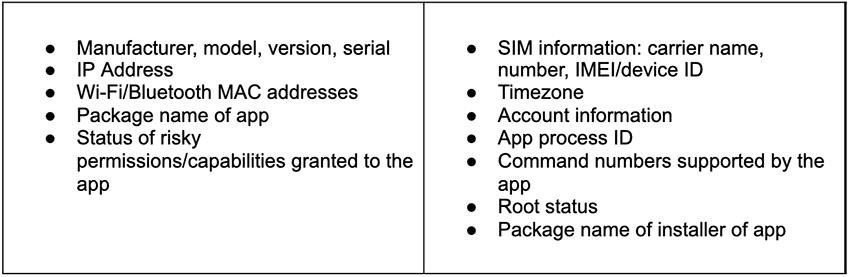
After installation AbstractEmu starts collecting and sending various system information to its command and control server and waits for further commands.
然之後, AbstractEmu operators can give the malware various commands, 例如, get root privileges, collect and steal files depending on how new they are or match a given pattern, and install new applications.
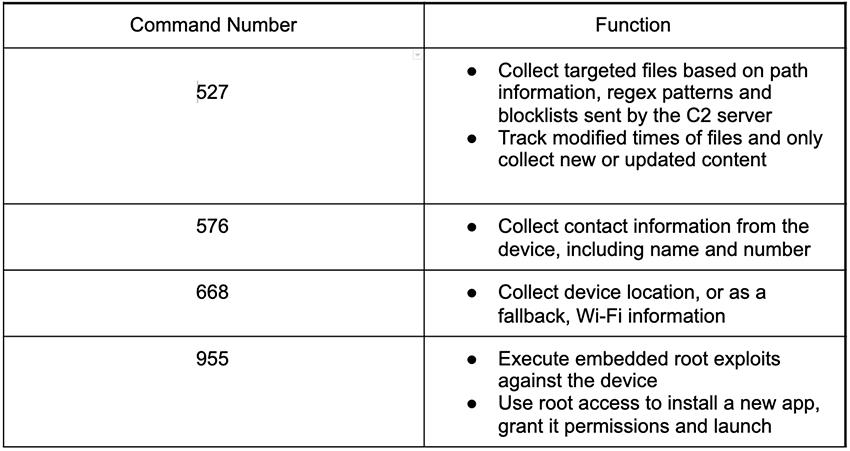
AbstractEmu has exploits for several known vulnerabilities in its arsenal to gain root privileges on infected devices. An expert report notes that one of the bugs, CVE-2020-0041, has never been used by Android apps before.
The malware also uses in attacks publicly available exploits for problems CVE-2019-2215 和 CVE-2020-0041, and vulnerability CVE-2020-0069, found in MediaTek chips, widely used by dozens of smartphone manufacturers and installed on millions of devices.
After rooting the device, AbstractEmu can track notifications, take screenshots and record video of the screen, or even block the device or reset its password.
讓我提醒你,我哋都寫過 Android malware GriftHorse infected over 10 million devices.




