טעאַבאָט מאַלוואַרע ינפילטרייץ Google פּלייַ סטאָר ווידער
די TeaBot באַנקינג טראָדזשאַן איז ווידער געפֿונען אין די Google פּלייַ סטאָר, ווו עס איז געווען אַ QR קאָד לייענער (QR קאָד & באַרקאָדע – סקאַננער) און געראטן צו פאַרשפּרייטן צו מער ווי 10,000 מכשירים. די מאַלוואַרע טאַרגאַץ ניצערס פון מער ווי 400 באַנקינג און פינאַנציעל אַפּלאַקיישאַנז, אַרייַנגערעכנט די פון רוסלאַנד, כינע, און די פארייניקטע שטאטן.
לויט א באַריכט פון קלעפי, טעבאָט-ינפעקטאַד אַפּלאַקיישאַנז אַקט ווי דראַפּערז. אַז איז, זיי באַקומען צו די Google פּלייַ סטאָר אָן בייזע קאָד און בעטן מינימאַל פּערמישאַנז פון די באַניצער, אַזוי אַז עס איז שווער פֿאַר ריוויוערז און Google ס אָטאַמייטיד טשעקס צו דעטעקט עפּעס סאַספּישאַס.
אין צוגאב, טראָודזשאַניזעד אַפּלאַקיישאַנז אַקשלי אַרבעט, דעליווערינג די צוגעזאגט פאַנגקשאַנאַליטי, אַזוי די באריכטן וועגן זיי זענען מערסטנס positive.
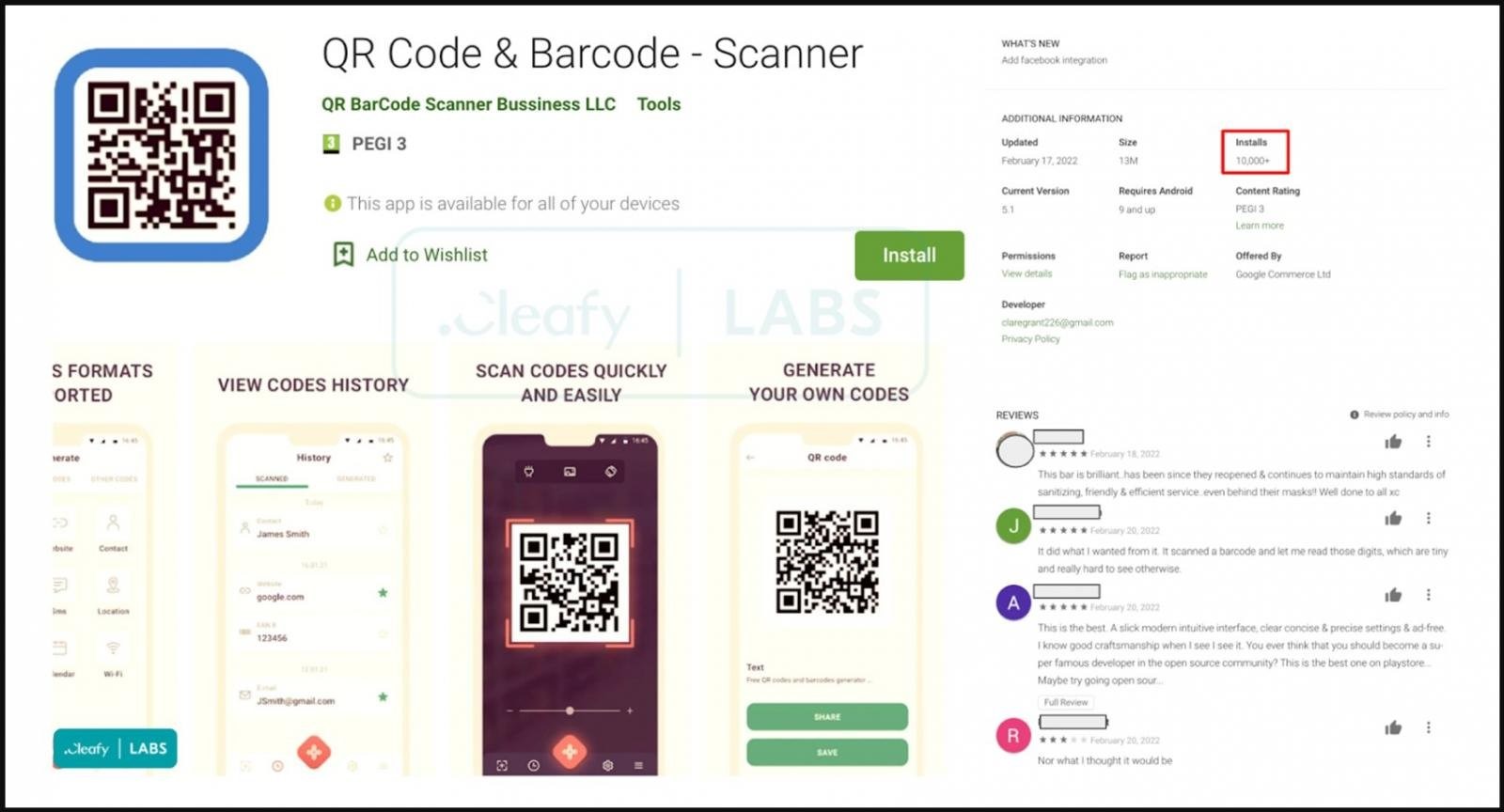
פֿאַר בייַשפּיל, QR קאָד & באַרקאָדע - סקאַננער וואָס איז געווען דיסקאַווערד אין פעברואר, געקוקט ווי אַ רעגולער נוצן פֿאַר סקאַנינג QR קאָודז. אָבער, אַמאָל אינסטאַלירן, די אַפּ געבעטן אַ דערהייַנטיקן דורך אַ קנאַל-אַרויף אָנזאָג, און אַנשטאָט פון די נאָרמאַל פּראָצעדור באַשטימט דורך די שפּיל סטאָר כּללים, דער דערהייַנטיקן איז דאַונלאָודיד פון אַ פונדרויסנדיק מקור.
די עקספּערץ טרייסט די מקור פון די דאַונלאָודז צו צוויי גיטהוב ריפּאַזאַטאָריז אָונד דורך די באַניצער felanicusor און מיט עטלעכע סאַמפּאַלז פון די TeaBot מאַלוואַרע, ופּלאָאַדעד אויף פעברואר 17, 2022.
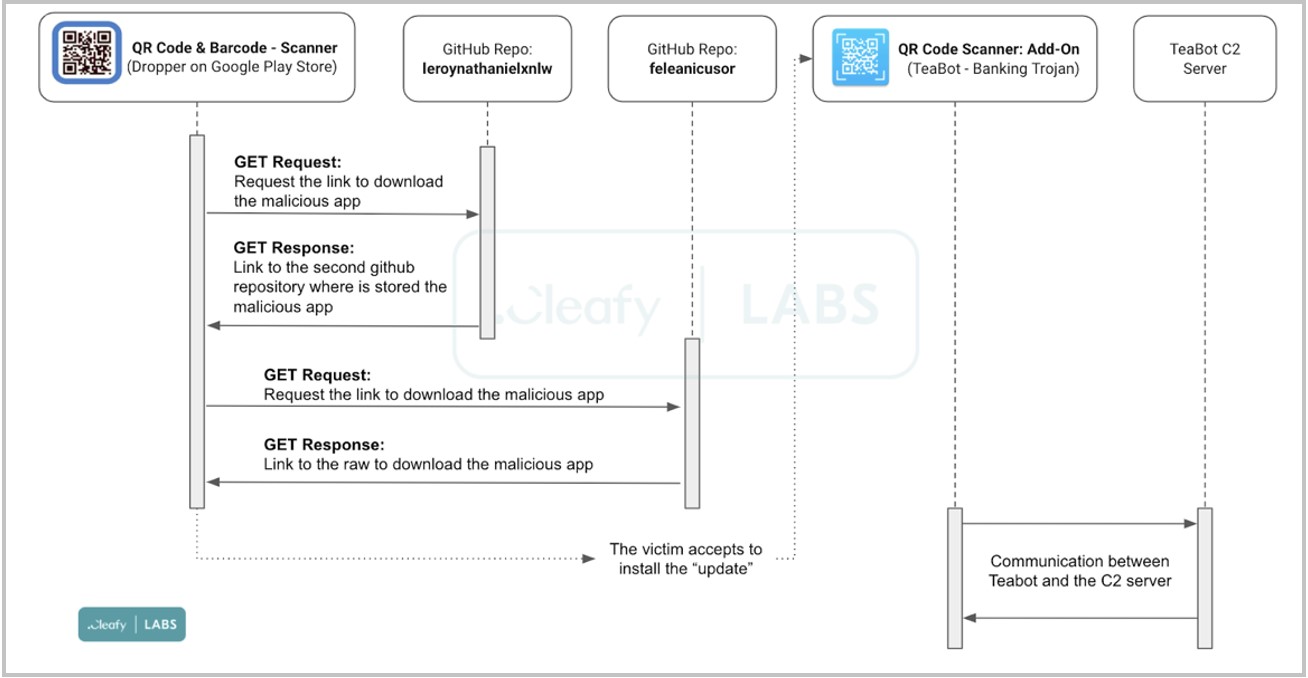
באַפאַלן סכעמע
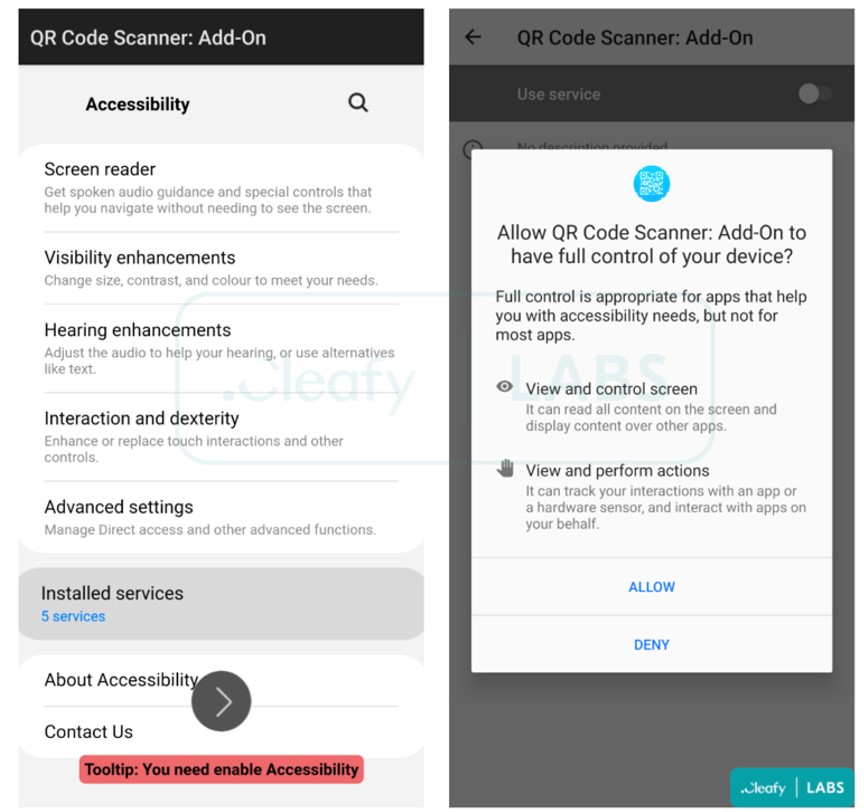
אַמאָל דעם “דערהייַנטיקן” איז גאַנץ, TeaBot איז דאַונלאָודיד צו די קאָרבן ס מיטל ווי אַ נייַ QR קאָד סקאַננער: לייג-אויף אַפּלאַקיישאַן. די אַפּלאַקיישאַן סטאַרץ אויטאָמאַטיש און ריקוועס די רעכט צו נוצן אַקסעסאַביליטי באַדינונגס צו דורכפירן די פאלגענדע פאַנגקשאַנז:
- קוק די מיטל פאַרשטעלן און שאַפֿן סקרעענשאָץ וואָס ווייַזן לאָגין קראַדענטשאַלז, צוויי-פאַקטאָר אָטענטאַקיישאַן קאָודז, SMS אינהאַלט, און אזוי ווייטער;
- אָטאַמאַטיק גראַנטינג פון נאָך פּערמישאַנז צו מאַלוואַרע אין דער הינטערגרונט, וואָס טוט נישט דאַרפן באַניצער אריינמישונג.
ינטערעסטינגלי, פריער ווערסיעס פון TeaBot, דיסקאַווערד אין יאנואר 2021 און געלערנט דורך ביטדעפענדער, ארויס אויב זיי דיטעקטאַד אַז די קאָרבן איז געווען אין די פאַרייניקטע שטאַטן. איצט TeaBot אויך אַטאַקס יוזערז פון די פאַרייניקטע שטאַטן, און אויך באקומען שטיצע פאר רוסיש, סלאָוואַקיש און כינעזיש שפּראַכן, דאס איז, די מאַלוואַרע אַטאַקס קיין ניצערס אָן מאכן אויסנעמען.
לאמיך אייך דערמאנען, אז מיר האבן דאס אויך געשריבן עקספּערץ דיסקאַווערד קסענאָמאָרף מאַלוואַרע אין די Google פּלייַ סטאָר, און אַז אַבסטראַקט עמו אַנדרויד מאַלוואַרע "רוץ" סמאַרטפאָנעס און יוויידז דיטעקשאַן.




