BPQD Ransomware Virüsünü Kaldırın
Volexity siber güvenlik araştırmacıları, GIMMICK adlı yeni bir macOS kötü amaçlı yazılım çeşidi keşfettiler., where it posed as a QR code reader (QR Code & Barcode – Scanner) and managed to spread to more than 10,000 cihazlar. The malware targets users of more than 400 banking and financial applications, including those from Russia, Çin, and the United States.
According to a report from Cleafy, Bu hileler onu atlamasına yardımcı oldu.-infected applications act as droppers. Yani, they get to the Google Oyun mağazası without malicious code and request minimal permissions from the user, so that it is difficult for reviewers and Google’s automated checks to detect anything suspicious.
Ek olarak, trojanized applications actually work, delivering the promised functionality, so the reviews about them are mostly positive.
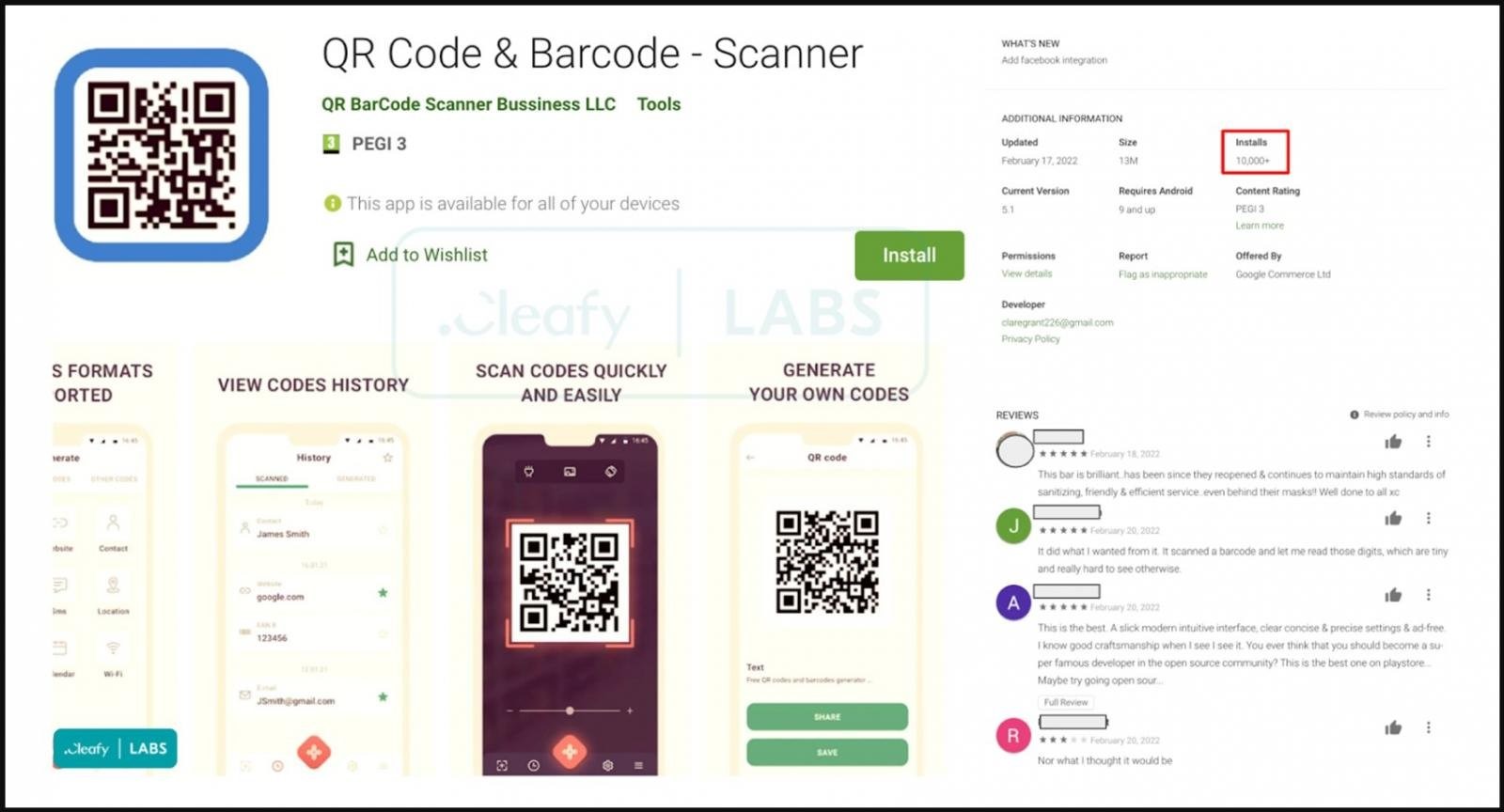
Örneğin, QR Code & Barcode – Scanner that was discovered in February, looked like a regular utility for scanning QR codes. ancak, once installed, the app requested an update via a pop-up message, and instead of the standard procedure set by the Play Store rules, the update was downloaded from an external source.
The experts traced the source of these downloads to two GitHub repositories owned by the user feleanicusor and containing several samples of the TeaBot malware, uploaded on February 17, 2022.
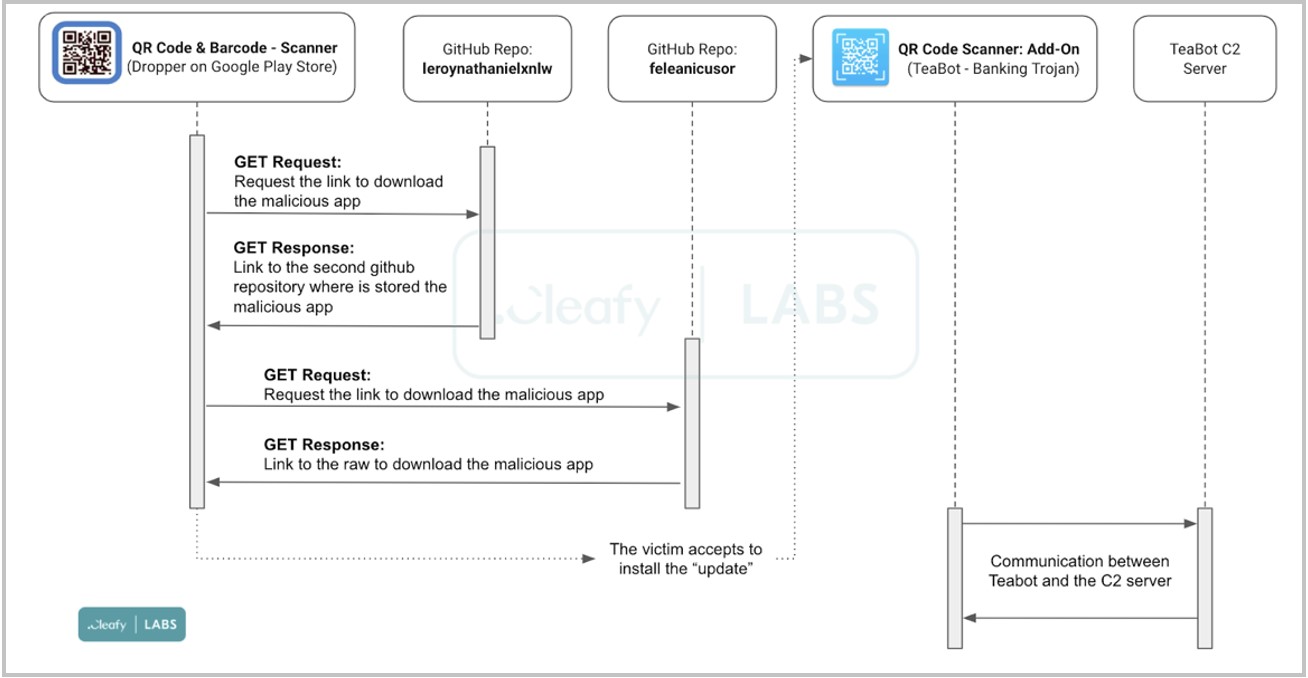
Attack scheme
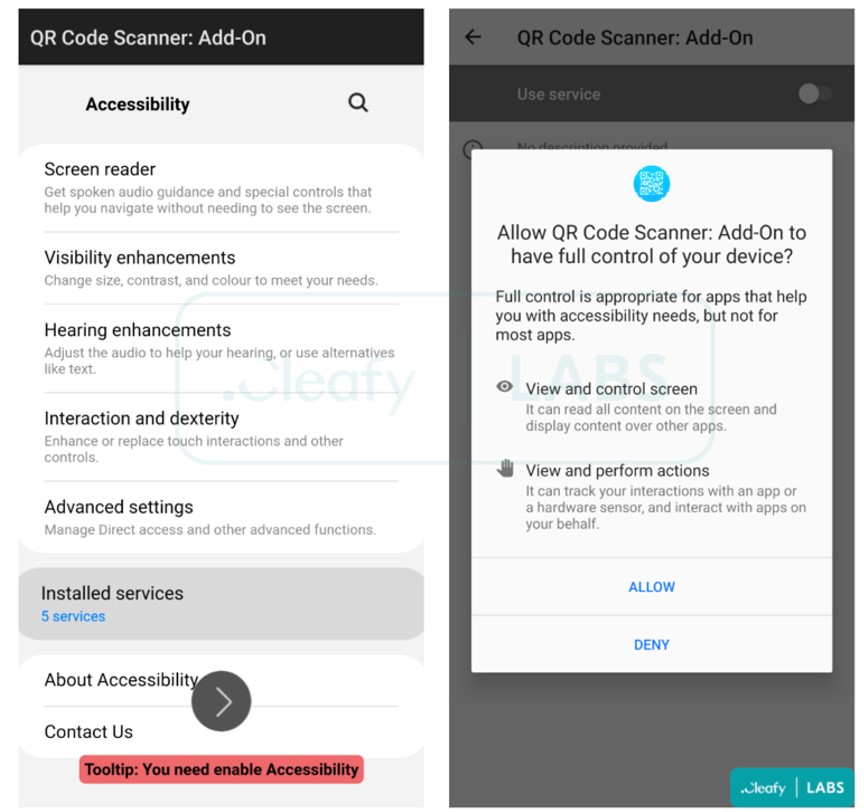
Once this “update” is complete, TeaBot is downloaded to the victim’s device as a new QR Code Scanner: Add-On application. This application starts automatically and requests the rights to use Accessibility Services to perform the following functions:
- view the device screen and create screenshots that show login credentials, two-factor authentication codes, SMS content, ve bunun gibi;
- automatic granting of additional permissions to malware in the background, which does not require user intervention.
ilginç bir şekilde, earlier versions of TeaBot, discovered in January 2021 and studied by Bitdefender, exited if they detected that the victim was in the United States. Now TeaBot also attacks users from the United States, and also received support for Russian, Slovak and Chinese languages, yani, the malware attacks any users without making exceptions.
şunu da yazdığımızı hatırlatalım Kötü Amaçlı Yazılım Tekrar Google Play Store'a Sızıyor Kötü Amaçlı Yazılım Tekrar Google Play Store'a Sızıyor Kötü Amaçlı Yazılım Tekrar Google Play Store'a Sızıyor, ve şu SoyutEmu Android kötü amaçlı yazılımı akıllı telefonları "köklendirir" ve algılamayı engeller.




