Navorsers het ALPHV losprysware ontdek wat in Rust geskryf is
Analysts from Opgeneem Toekoms en MalwareHunterTeam have discovered an ALPHV (alias BlackCat) ransomware with executable file is written in Rust, which is atypical for malware, but this approach is gradually gaining popularity among cybercriminals due to its high performance and memory security.
The malware developers themselves call it ALPHV and actively promote their malware on Russian-language hack forums. Egter, due to the fact that the cybercriminals’ website uses an icon depicting a black cat, the researchers dubbed the malware Swart kat.
Technically, this ransomware is already the third ransomware written in Rust: PoC malware of this kind was published on GitHub in 2020, and the already inoperative BadBeeTeam ransomware was spotted in the same year.
Egter, the researchers write that against their background, ALPHV (Swart kat) looks like the first professional RaaS malware aimed at corporate hacking and device encryption. Byvoorbeeld, recently a well-known cybersecurity specialist and Emsisoft analyst Michael Gillespie, described BlackCat as a “very complex” ransomware.
Volgens Opgeneem Toekoms kenners, die skepper van ALPHV (Swart kat) was previously a member of the well-known hacker group ERWEL. Since early December, this man (known as ALPHV) has been promoting RaaS on underground forums (XSS and Exploit), inviting other criminals to join ransomware attacks against large companies. The attacker claims that the malware can encrypt data on systems running Windows, Linux and VMware ESXi, and partners will receive from 80% aan 90% of the final ransom, depending on the total amount received from the victims.
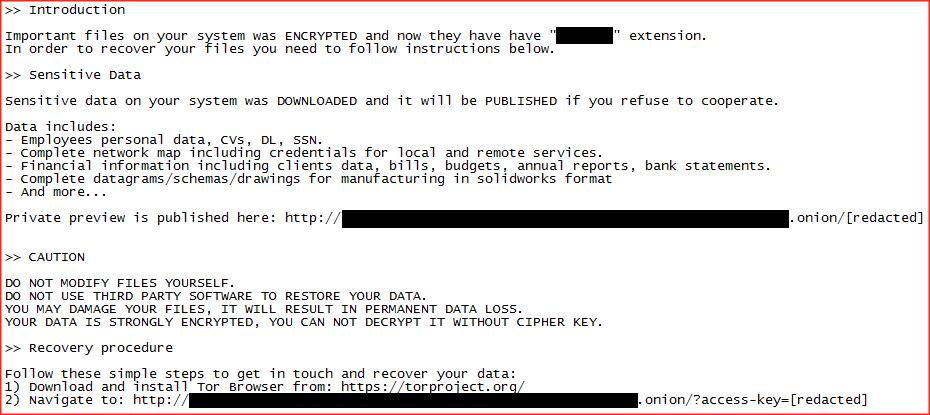
So far, experts do not know exactly how the malware penetrates the victim’s systems, but like most other ransomware groups, the ALPHV (Swart kat) operators are engaged in double extortion. Dit is, before encrypting files, hackers search the victim’s network for confidential data, steal it, and then demand a ransom, otherwise they threaten to publish the stolen data in the public domain (or sell it to interested parties).
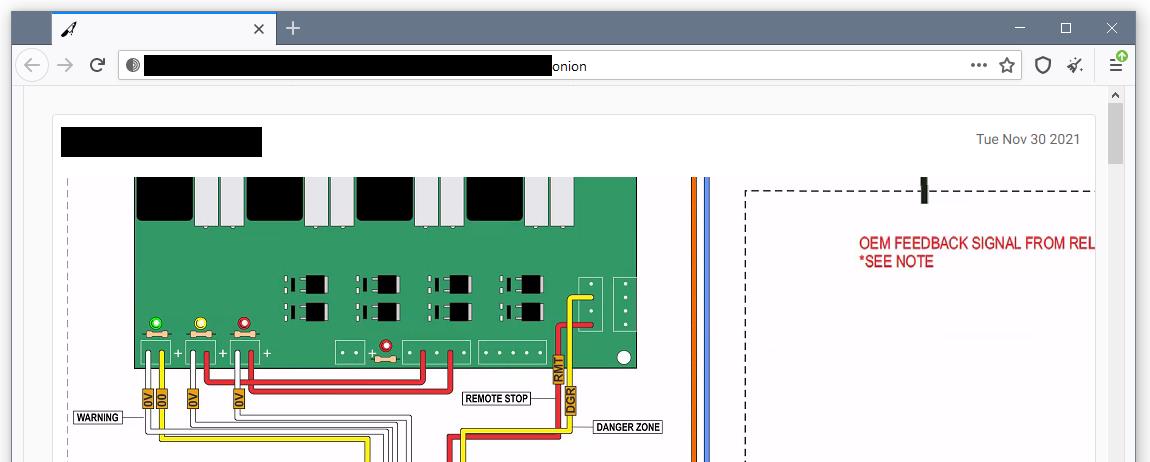
Tans, the group seems to be managing several “leak sites” at once, each of which stores the data of one or two victims. A screenshot of one of these sites can be seen below. It looks like these sites are being served by the team partners themselves, which explains the different urls.
Bliepende rekenaar reports that since November 2021, many companies in the USA, Australia and India have become victims of this ransomware. The journalists’ own sources say the ransom size ranges from $ 400,000 aan $ 3,000,000 (in Bitcoin or Monero). If victims pay with Bitcoin, an additional 15% commission is added to the ransom.
Laat ek u daaraan herinner dat ons dit ook berig het Grief ransomware threatens to destroy victims’ data as hulle hulle tot onderhandelaars wend.




