GoodWill Afperser dwing slagoffers tot goeie dade
CloudSek specialists talked about a strange GoodWill ransomware that does not demand money from the victims, but forces them do good deeds in exchange for decrypting files.
Byvoorbeeld, ransomware operators are told to distribute clothes to the homeless or pay medical bills to those who need urgent medical care but cannot afford it.
Let me remind you that we wrote about The Appearance of Cheap DarkCrystal RAT Malware Worried Experts, En ook dit Microsoft Warns of Increased XorDdos Malware Activity.
According to the researchers, GoodWill is predominantly distributed in India and, apparently, was created in the same country. It is likely that the ransomware is someone’s experiment, since so far, the experts have not been able to detect a single GoodWill victim.
This malware was first noticed in March 2022. It is known that GoodWill is written in .NET and seems to be built on the basis of the open-source malware HiddenTear. After infecting the system, it sits idle for 722.45 seconds to confuse dynamic analysis and also uses the AES_Encrypt function to encrypt using AES.
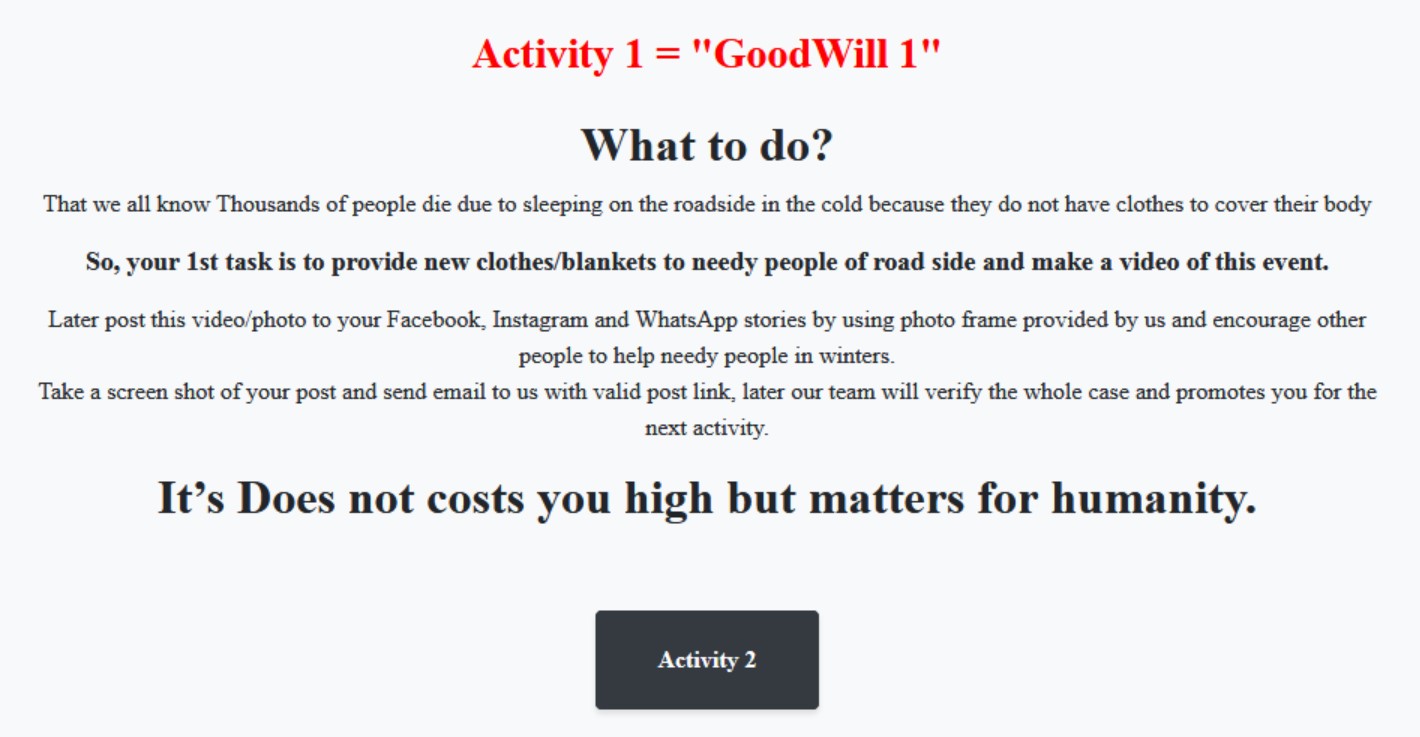
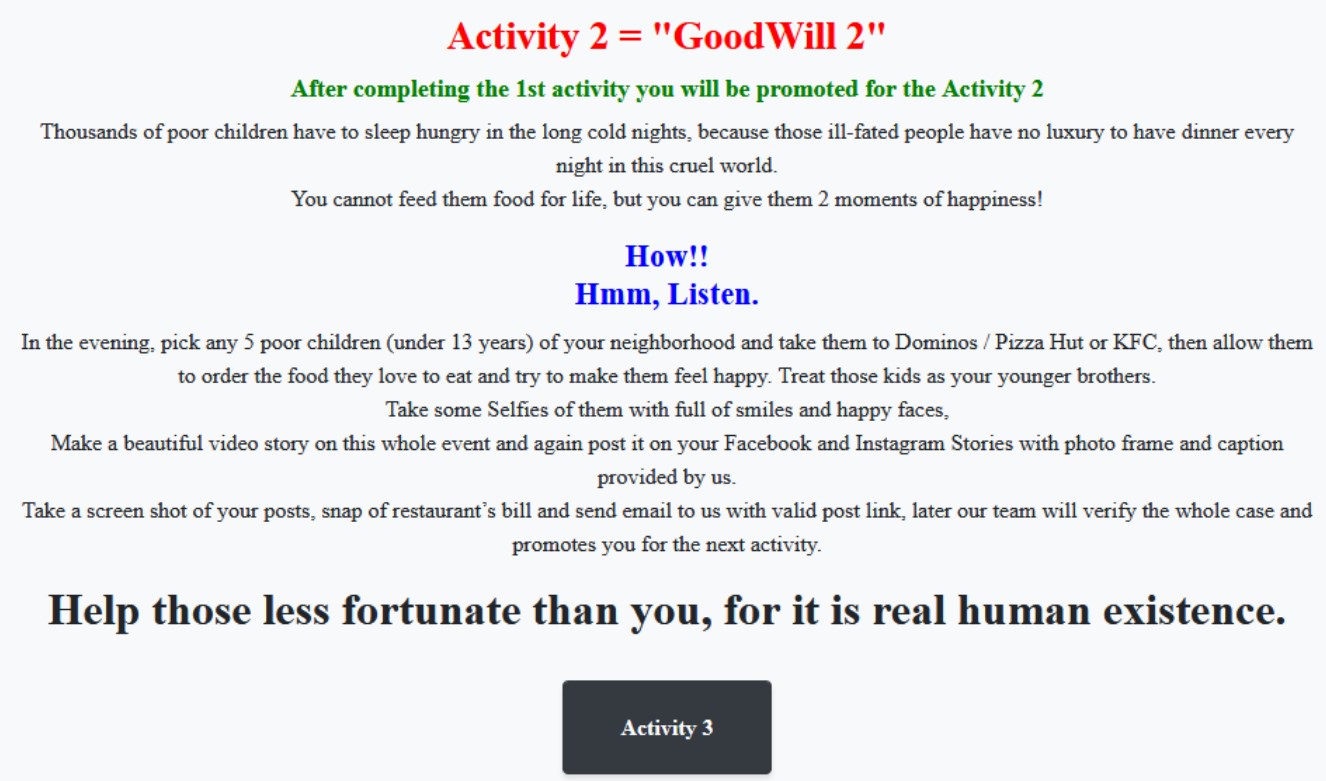
After infection, GoodWill encrypts all documents, photos, videos, databasisse, and other important files and leaves a note asking victims to do three good deeds to get the key to decrypt the data. Dus, malware operators require:
- donate new clothes to the homeless, record it on video and post it on social networks;
- take at least five children from disadvantaged families to Dominos, Pizza Hut of KFC and feed them, take photos and videos of the process and post them on social networks;
- provide financial assistance to those who need urgent medical care but cannot afford it, record the entire conversation and share the audio recording with GoodWill operators.
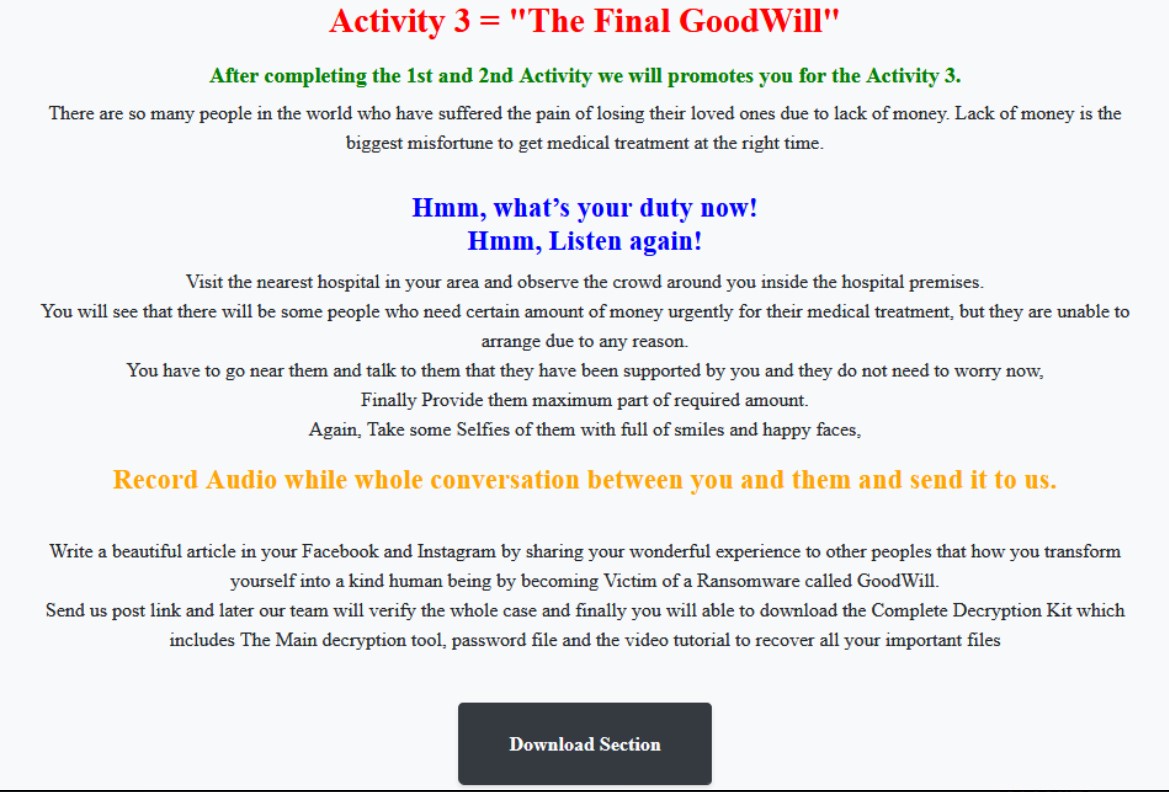
After completing all these actions, the victim should also write another post on social networks, talking about “turning into a kind person after becoming a victim of the GoodWill ransomware.”




