Nuwe Botnago Botnet gebruik 33 Ontgin teen IoT -toestelle
AT&T experts ontdek het a new botnet BotenaGo. The malware uses more than thirty exploits to attack routers and other Internet of Things devices.
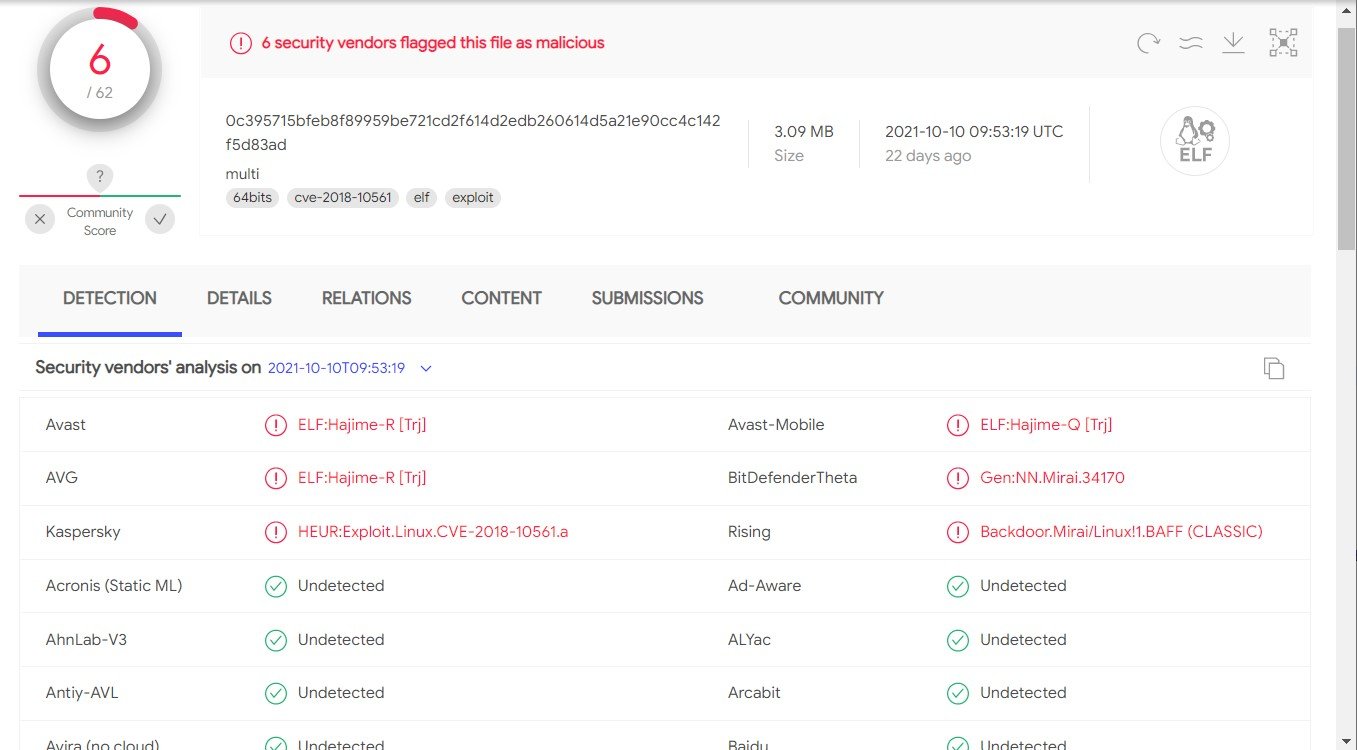
As the name implies, the botnet is written in the Golang (Go) language, which has become increasingly popular among malware developers in recent years. Only 6 uit 62 antivirus products on VirusTotaal identify Botenago as malware (with some identifying it as a Mirai variation).
The researchers say that BotenaGo gebruike 33 exploits for various routers, modems and NAS devices. Among them there are exploits for the following problems:
- CVE-2015-2051, CVE-2020-9377, CVE-2016-11021: D-Link routers;
- CVE-2016-1555, CVE-2017-6077, CVE-2016-6277, CVE-2017-6334: Netgear toestelle;
- CVE-2019-19824: Realtek SDK based routers;
- CVE-2017-18368, CVE-2020-9054: Zyxel routers and NAS;
- CVE-2020-10987: Tenda Products;
- CVE-2014-2321: ZTE Modems;
- CVE-2020-8958: 1GE ONU.
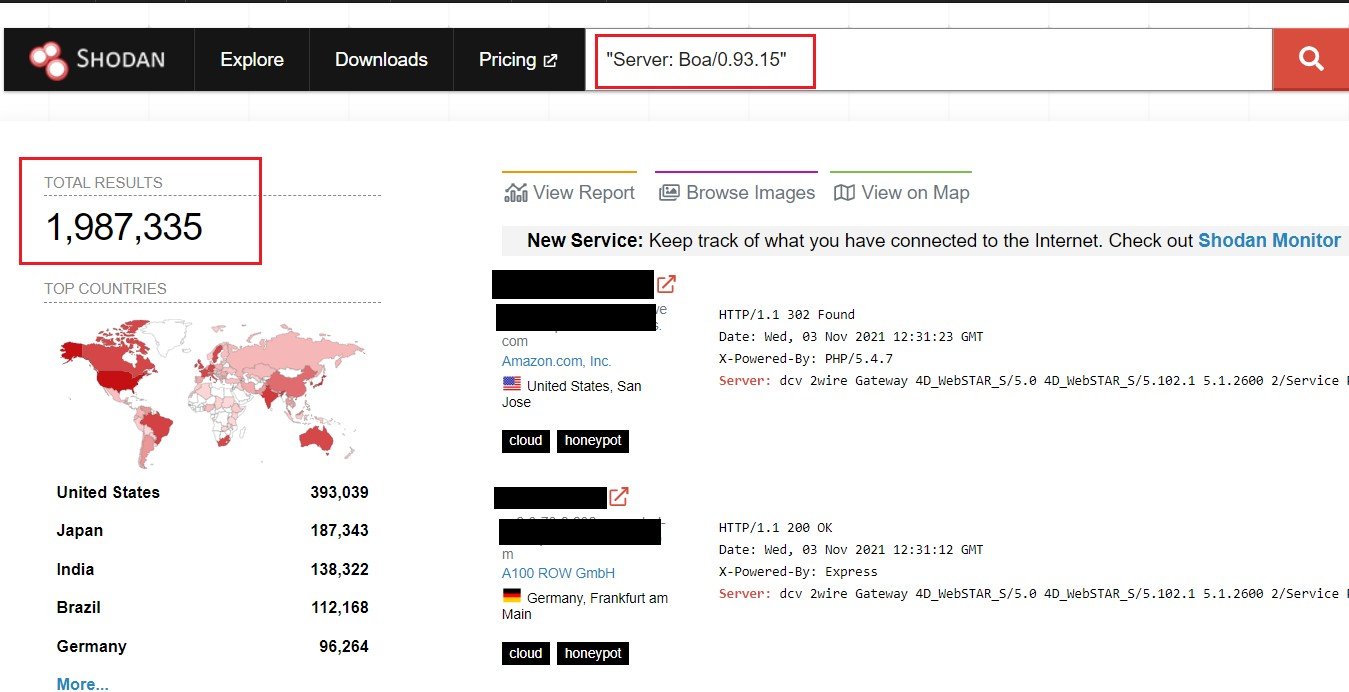
Due to so many exploits, malware is capable of attacking millions of devices. Byvoorbeeld, experts write that, according to Shodan, the vulnerable open-source Boa web server alone, whose support has already been discontinued, is still used by more than two million devices.
Die AT&T report states that the malware uses different links to receive payloads, depending on the device being attacked. Ongelukkig, during the study of the malware, there were no payloads on the server at all, so it was not possible to study them.
Daarby, the researchers write that they have not yet found active communications between BotenaGo and the server controlled by the attackers. They give three possible explanations for this:
- BotenaGo is only a part (module) of a multi-stage modular attack, and it is not at all responsible for communicating with the C&C bediener.
- BotenaGo is a new tool used by Mirai operators on certain machines. This theory is supported by general references for payloads.
- Malware is not ready for work yet, and the sample accidentally got into the network.
Laat ek jou herinner dat ek dit ook geskryf het Pienk botnet is infected over 1.5 miljoen toestelle, as well as that MYKINGS Botnet steel cryptocurrency via knipbord.




