MyKings botnet krade kriptovaluto prek odložišča
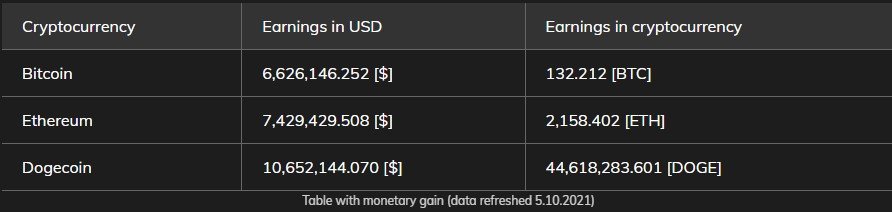
MyKings botnet (aka Smominru in DarkCloud) je še vedno aktiven in krade kriptovalute, while its operators “earn” huge sums. Po navedbah Avast research, cybercriminals’ wallets hold at least $ 24 million in Bitcoin, Ethereum, and Dogecoin.
It is not known if all the funds were stolen from MyKings, but at least some of this amount was definitely obtained using this botnet.
MyKings is one of the most analyzed botnets in recent years, and it is especially interesting for researchers due to its extensive infrastructure and numerous features, including bootkits, miners, droppers, clipboard data stealing solutions and much more.
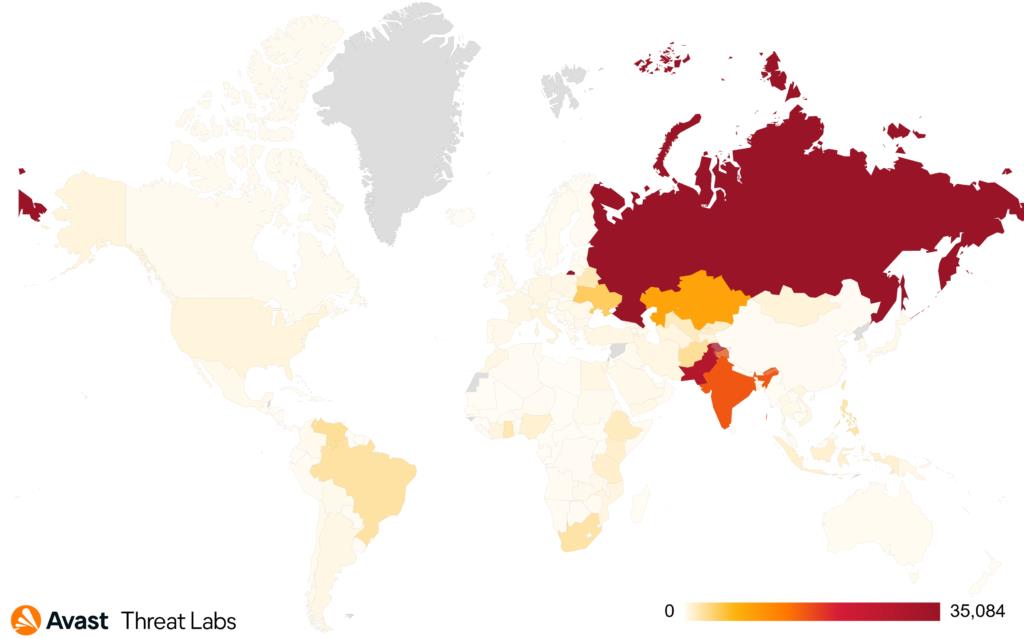
Analysts at Avast Threat Labs say they have collected over 6,700 unique MyKings samples for analysis (since the beginning of 2020). During the same period, Avast products protected more than 144,000 users from this malware, and most of the attacks occurred in Russia, India and Pakistan.
The way MyKings works is very simple: after installation, the malware keeps track of what the victim is copying to the clipboard. Having found the address of the user’s cryptocurrency wallet in the buffer, the malware replaces it with the address of the wallet of its operators. Po tem, when the victim inserts from the buffer (as he thinks) the correct address of his crypto wallet, he is actually inserting the address of the criminals’ wallet. torej, the cryptocurrency is sent to the pockets of the attackers.
The botnet uses many cryptocurrency wallets, some of which are quite high in value. Avast reports that the cryptocurrency in these wallets was collected mainly by spoofing addresses in the clipboard, as well as mining.
Let me remind you that I also told that Zlonamerna programska oprema BloodyStealer ugrabi Steam, Računa Epic Games Store in EA Origin.




