Cross-platform SysJoker-agterdeur val Windows aan, macOS en Linux
Intezer experts ontdek het a new cross-platform SysJoker backdoor that is used against devices on Windows, Linux and macOS as part of a cyberspy campaign.
According to researchers, the malware has been active since at least the second half of 2021. The malware was first discovered in December 2021 during an attack on a Linux-based web server owned by an unnamed educational institution.
The malware is written in C++ and each variant is adapted for a specific operating system. Egter, all variations are not detected by the security solutions presented on VirusTotaal.
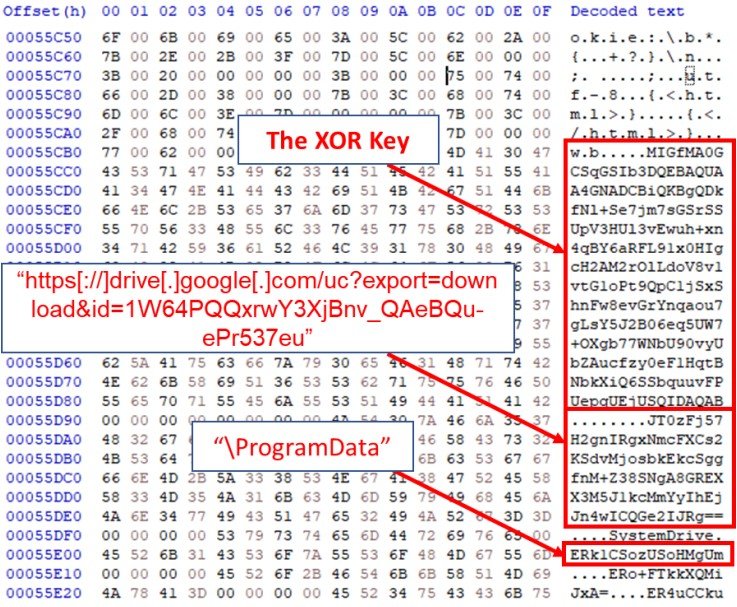
On Windows, SysJoker uses a first-level dropper in DLL format, which then executes PowerShell commands and does the following: Gets the SysJoker ZIP file from the GitHub repository, extracts it to C:\ProgramData\RecoverySystem\, and executes the payload. The malware is idle for about two minutes before it creates a new directory and copies itself as Intel Graphics Common User Interface Service (igfxCUIService.exe).
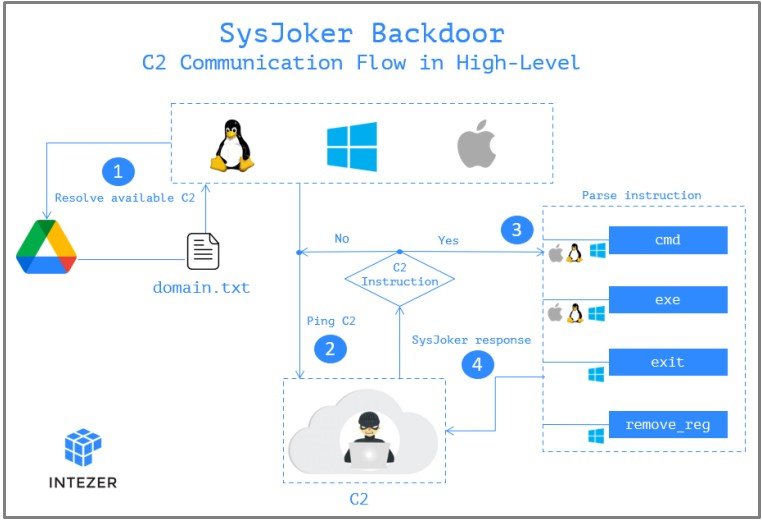
After collecting the data, the malware will gain a foothold in the system by adding a new registry key (HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run). The next step is the aforementioned call to the management server, which uses a hardcoded link to Google Drive.
When the information collected during the first stages of infection is sent to the C&C bediener, it responds with a unique token, which later serves as the identifier of the infected machine. Ook, the control server can order the backdoor to install additional malware, execute specific commands on the infected device, or delete itself. It is noted that the last two functions have not yet been fully implemented.
The researchers write that the Linux and macOS versions do not have a DLL dropper, but generally perform the same malicious operations on the infected device.
You might be interested to know what Die Capoes malware installs a backdoor plugin on WordPress sites, en dit Nuut XLoader malware steals credentials from macOS and Windows.




