The Capoae malware installs a backdoor plugin on WordPress sites
Akamai experts write that Capoae malware infiltrates WordPress sites, installs a plugin with a backdoor on them, and then uses the system to mine cryptocurrency.
Expert Larry Cashdollar warns that the main tactic of such malware is spreading through vulnerable systems, as well as cracking unreliable administrator credentials. The studied sample of the malware Keshdollar named Capoae.
This malware is delivered to hosts running WordPress via the download-monitor plugin with a backdoor, which cybercriminals install on sites after successfully brute-forcing credentials.
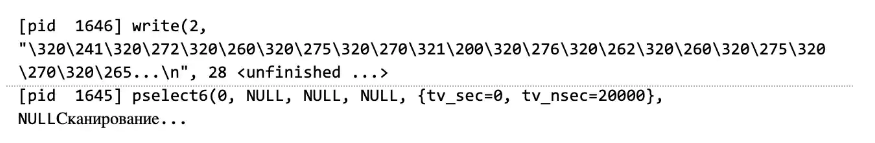
The attack also involves deploying a binary to Golang, whereby the obfuscated payload is retrieved via a GET request, which the malicious plugin makes to the attacker’s domain.
The malware can also decrypt and execute other payloads: basically, the Golang binary exploits various RCE vulnerabilities in Oracle WebLogic Server (CVE-2020-14882), NoneCms (CVE-2018-20062) and Jenkins (CVE-2019-1003029 and CVE-2019-1003030) in order to brute force and not only work its way into the system and ultimately launch the XMRig miner.
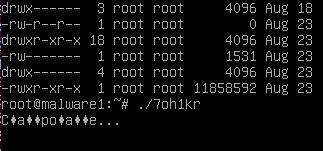
Attackers do not forget that they need to act unnoticed. To do this, they use the most suspicious-looking paths on the disk and directories where real system files can be found, and also create a file with a random six-digit name, which is then copied to another location (before deleting the malware after execution).
Let me remind you that I also wrote that Researchers warned of new DarkRadiation ransomware.




