DoppelPaymer 勒索軟件更名為 Grief
嗶嗶電腦 寫 DoppelPaymer勒索軟件運營商已將其產品“更名”,現在惡意軟件被更名為悲傷 (或付出或悲傷).
Doppelpaymer的活動在Darkside Ransomware在Colonial Pipeline Company的醜聞襲擊之後幾乎毫無意義, 之後 它被禁止 在最大的黑客論壇上做廣告和討論勒索軟件, 許多小組寧願退後一會兒.
EMSISOFT專家Fabian Vosar是第一個引起流放計算機注意的事實,即悲傷和Doppelpaymer是同一威脅. 儘管攻擊者試圖使悲傷與Doppelpaymer不同, 相似性對於專家來說仍然很明顯. 特別是, 黑客使用相同格式用於加密文件和相同的惡意軟件分發頻道 – Dridex殭屍網絡.
悲傷的第一個消息是在6月初 (儘管在5月發現了一個樣本 17), 然後研究人員認為這是一個新的威脅.
但是現在, ZScaler 已經檢查了 早期的悲傷樣本,並註意到贖金紙幣指向DoppelPaymer網站, 由於悲傷的網站顯然還沒有準備好.
眼下, 在悲傷網站上, 您已經可以找到對兩打受害者的參考, 雖然Doppelpaymer網站自5月以來尚未更新 2021.
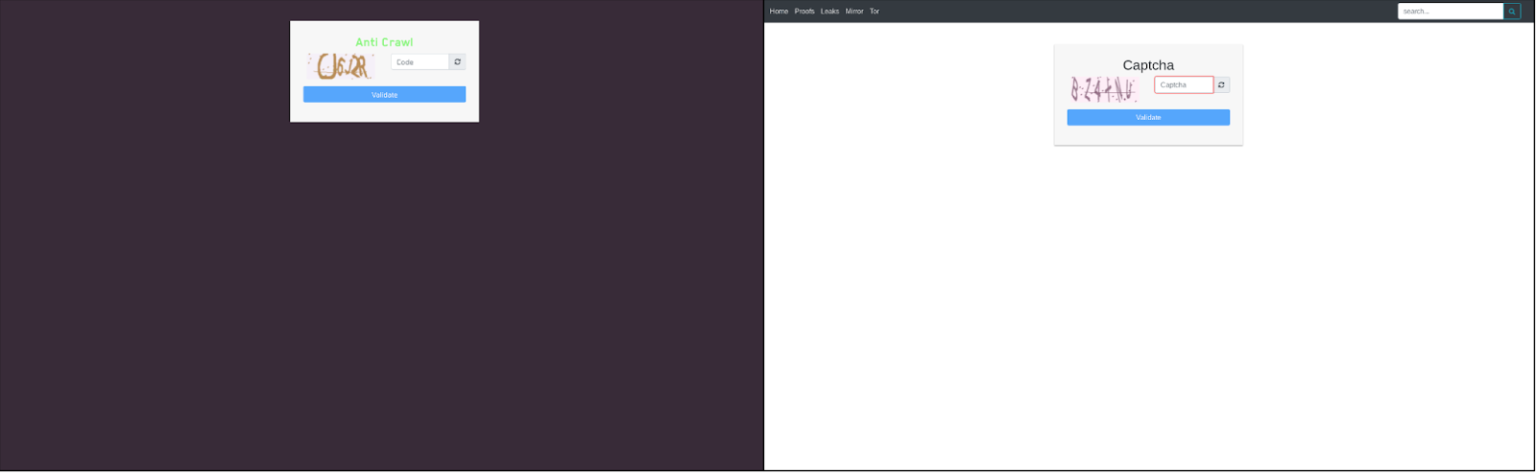
甚至勒索軟件網站上的驗證碼也相同.
此外, 注意到這兩個惡意軟件均基於非常相似的代碼, 記者強調,目前沒有證據表明支付贖金一般會導致收到鑰匙, 例如, 工具 “相同的加密算法 (2048-位RSA和256位AES) 和進口哈希。” 也, 悲傷和Doppelpaymer都使用GDPR向受害者施加壓力,並提醒他們,如果數據洩露情況, 他們將不得不面對法律後果.
Grief Ransomware是Doppelpaymer勒索軟件的最新版本,具有較小的代碼更改和新外觀.ZScaler說.
並補充說,黑客最近一直保持低調,以避免Revil勒索軟件在黑客客戶攻擊後收到的不必要的關注. 卡西亞, 和殖民管道攻擊後的黑暗方向.
讓我提醒你,我也寫過 研究人員將 TrickBot 開發人員與 Diavol 勒索軟件聯繫起來.




