專家分析了一個新嘅惡意軟件樣本並確認了REvil返回
喺俄美關係日益緊張嘅背景的, experts analysed samples of the new malware and confirmed the return of REvil cybercriminals with a new ransomware.
After the start of Russia’s invasion of Ukraine, REvil’s 職責範圍 sites began to revive, but they did not have the old information, they redirected visitors to the URLs of a new, unnamed ransomware hacker group.
While these sites were not like previous REvil sites, the fact that the old infrastructure was redirecting to new URLs points to the return of grouping. 然而, in November, messages “REvil is bad” began to appear on the group’s websites. Such access to hacker sites spoke of the actions of law enforcement agencies or cybercriminals, so the revived pages of REvil cannot serve as a strong evidence of the return of the gang.

The only way to know for sure if REvil was back was to find a sample ransomware and analyse it to determine if it was patched or developed from the source code. The right sample of the new ransomware was discovered this week by AVAST 研究員 Jakub Krustek. Analysis of the sample confirmed the connection of the unnamed group with REvil.
According to analysts, the discovered sample of the virus was compiled from the REvil source code, and also contains fresh changes. Security researcher R3MRUM tweeted that the sample’s version number has been changed to 1.0, but it is a continuation of the latest version, 2.08, released by REvil before it was destroyed.
The specialist could not explain why the virus does not encrypt files, but believes that it was compiled from source code.
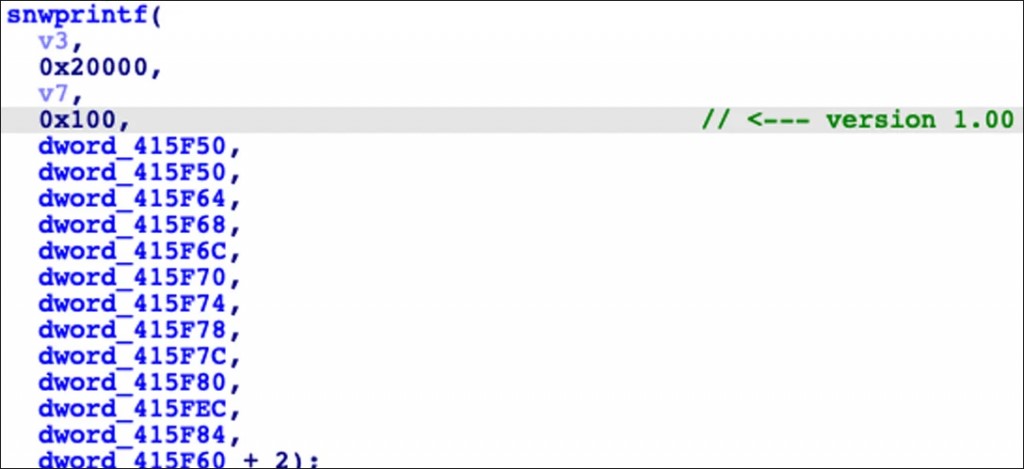
Version change in the new REvil encoder
Advanced Intel CEO Vitaly Kremez also examined the sample and confirmed that it was compiled from source on April 26th. According to him, the new REvil sample includes a new ‘accs’ configuration field containing the credentials of the attacked victim.
Kremez believes the ‘accs’ configuration option is used to prevent encryption on other devices that don’t contain the right Windows accounts and domains, allowing targeted attacks.
In addition to the “accs” 參數, the SUB and PID parameters used as Campaign and Branch IDs have been changed in the configuration of the new REvil sample to use longer GUID type values such as “3c852cc8-b7f1-436e-ba3b-c53b7fc6c0e4”.
BleepingComputer also tested a ransomware sample and it created a ransom note that is identical to the old REvil ransom warnings.
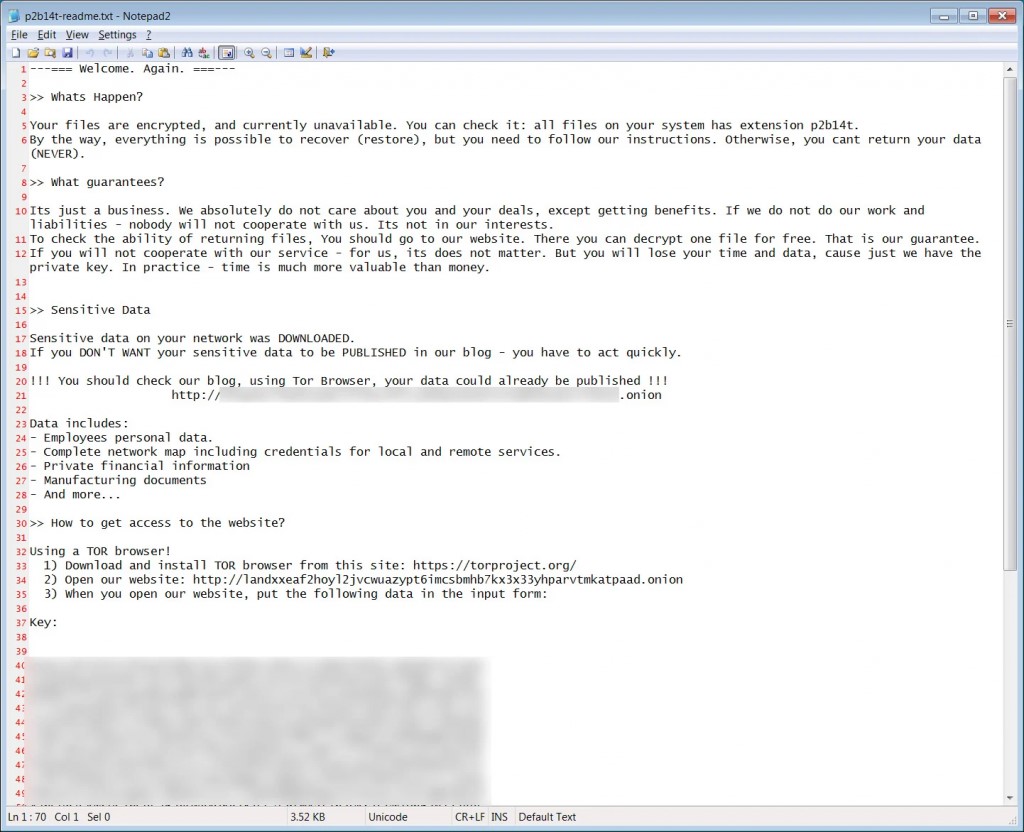
REvil ransom note
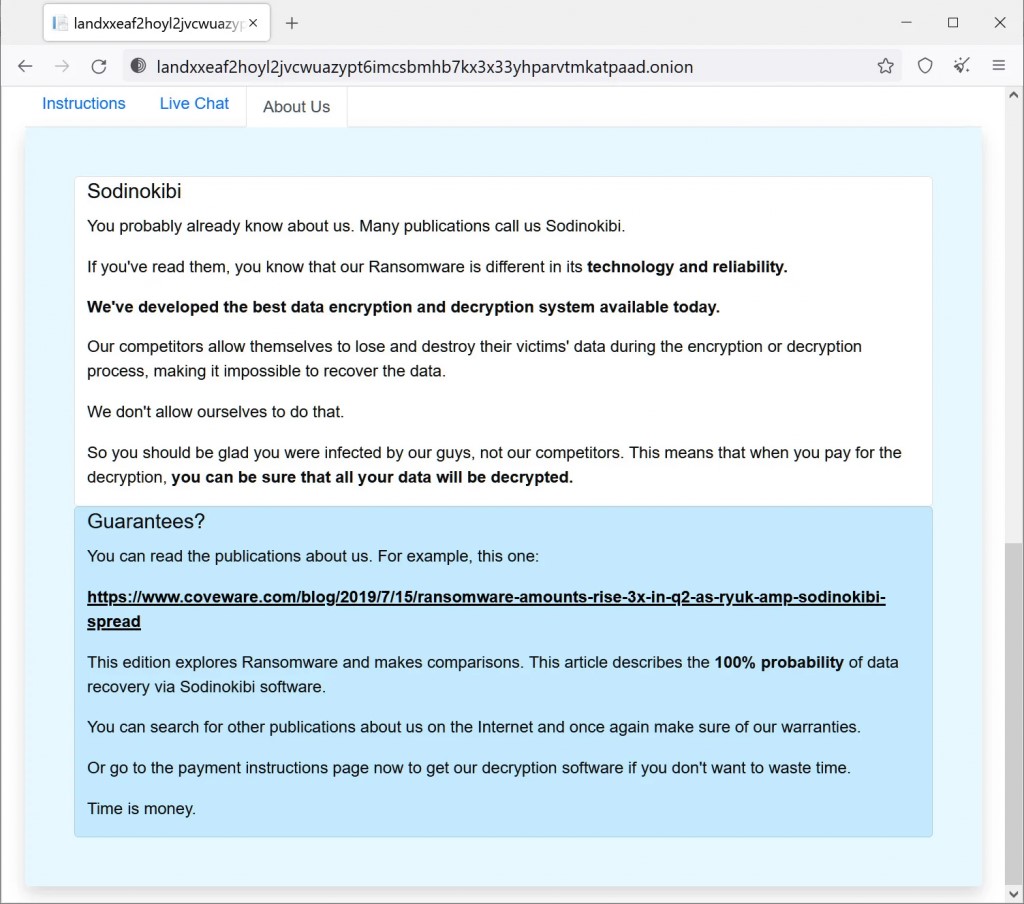
The new group calls themselves “Sodinokibi“, however the new site is almost identical to the old Revil site.
Not surprisingly, REvil has changed its name as part of the new operation, especially due to the worsening relations between the US and Russia.




