PatchWork Group đã vô tình lây nhiễm Trojan Ragnatela vào hệ thống của chính mình
Các nhà nghiên cứu bảo mật đã nhận thấy rằng một nhóm hack gián điệp mạng Ấn Độ có tên PatchWork (or Dropping Elephant, Chinastrats, or Quilted Tiger) has infected its own systems with the Ragnatela Trojan.
Các PatchWork group has been active since at least December 2015, and earlier experts have already noted that hackers use code copied from others.
During the latest PatchWork campaign, which ran from late November to early December 2021, Malwarebytes Labs observed that attackers used malicious RTF documents posing as Pakistani officials and infected their target systems with a new variant of BADNEWS RAT known as Ragnatela.
Ragnatela RAT is able to execute commands necessary for hackers, take screenshots, intercept keystrokes, collect confidential files and lists of running applications on the infected machine, deploy additional paylods and steal files.
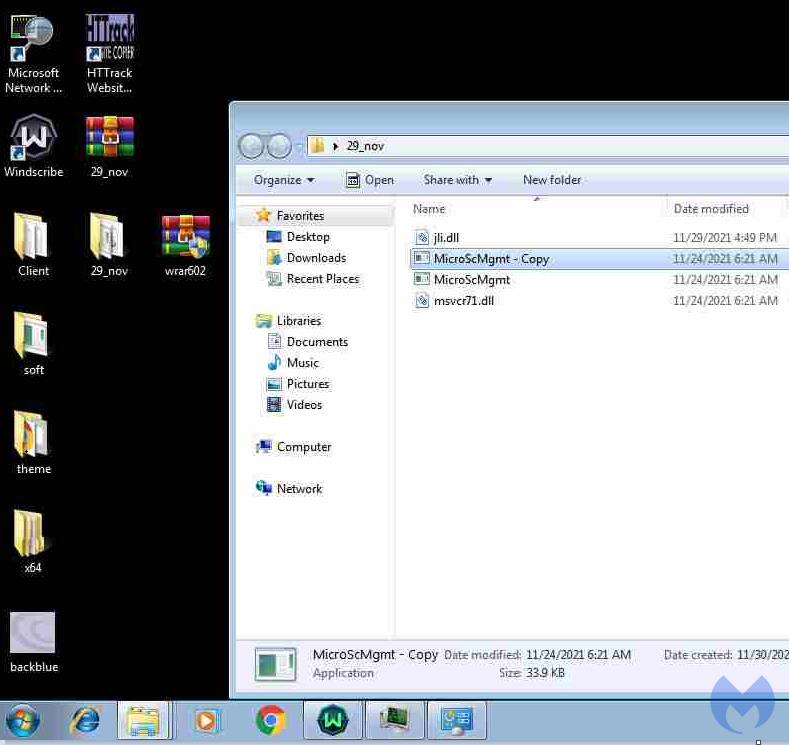
After discovering that the PatchWork operators had infected their own systems with malware, the researchers were able to track them using VirtualBox and VMware and collect more data on APT activity. Observing the group’s operations, experts gathered information on the targets of hackers, including the Pakistani Ministry of Defense, as well as professors in molecular medicine and biological sciences at several universities (including Pakistan’s National Defense University, UVAS University Biology Department, Karachi University and SHU University).
Let me remind you that recently we talked about another curious case when tiếp tục ransomware fell victim to a data leak.
You may also be interested to read about Rook’s new ransomware is that based on Babuk source code.




