Qrator Labs upptäckte ett nytt botnät för datautvinning
Chaes banker’s large-scale campaign was discovered, during which about 800 WordPress sites were compromised. The Trojan mainly targets Brazilian users and uses five malicious extensions for the Chrome browser in its attacks.
Chaes activity was discovered förbi Avast experter, who report that a new malware campaign started at the end of 2021. Initialt, the malware was discovered back in 2020 förbi Cybereason analytiker, and then (as now) it was aimed at customers of Banco do Brasil, Loja Integrada, Mercado Bitcoin, Mercado Livre and Mercado Pago banks.
Now the researchers say the attack starts when the victim visits one of the hacked sites. There, the user sees a pop-up window asking to install a fake Java Runtime Ansökan.

The MSI installer for this “app” contains three malicious files (install.js, sched.js, sucesso.js) that prepare the Python environment for the next stage loader. If the user follows the instructions, the malware initiates a complex bunker delivery procedure, which ends with the deployment of several modules – including spyware and remote-access module.
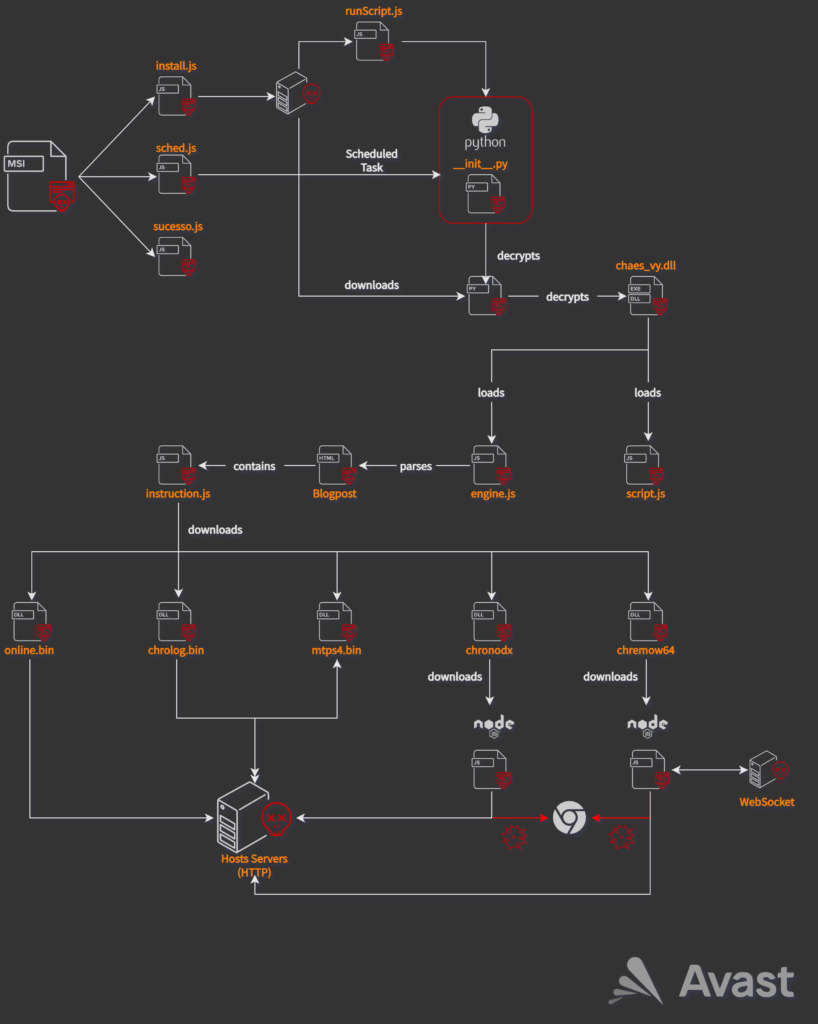
Some intermediate payloads are not only encrypted, but also hidden in commented code inside the HTML pages of the awsvirtual[.]blogspot.com domain. At the final stage of the attack, the JavaScript dropper downloads and installs up to five malicious Chrome extensions on the victim’s system:
- Online – Delphi module used to fingerprint the victim and transfer system information to the hackers’ control server;
- Mtps4 (MultiTela Pascal) is a Delphi-based backdoor, the main purpose of which is to connect to the control server and wait for the response Pascal Script to be executed;
- Chrolog (ChromeLog) – steals passwords from Google Chrome, the module is also written in Delphi;
- Chronodx (Chrome Noder) is a JavaScript Trojan that, upon detecting the launch of the Chrome browser, immediately closes it and opens its own instance of Chrome containing a malicious module that steals banking information;
- Chremows (Chrome WebSocket) is a banking JavaScript Trojan that intercepts keystrokes and mouse clicks in Chrome to steal credentials (for Mercado Livre and Mercado Pago users).
Låt mig påminna dig om att vi också skrev det Banking Trojan QakBot attacked over 17,000 användare över hela världen, och även det Anubis Android Banker Targets Nearly 400 Användare av finansiella appar.




