סרוז טרויאני ודרופר מופץ במסווה של 15 משחקים פופולריים
באפריל השנה, מומחי מעבדת קספרסקי recorded a large-scale campaign to distribute a Trojan and a dropper named Swarez.
The malware was distributed under the guise of 15 popular games, and attempts to download such files were recorded by the company’s products in 45 countries of the world.
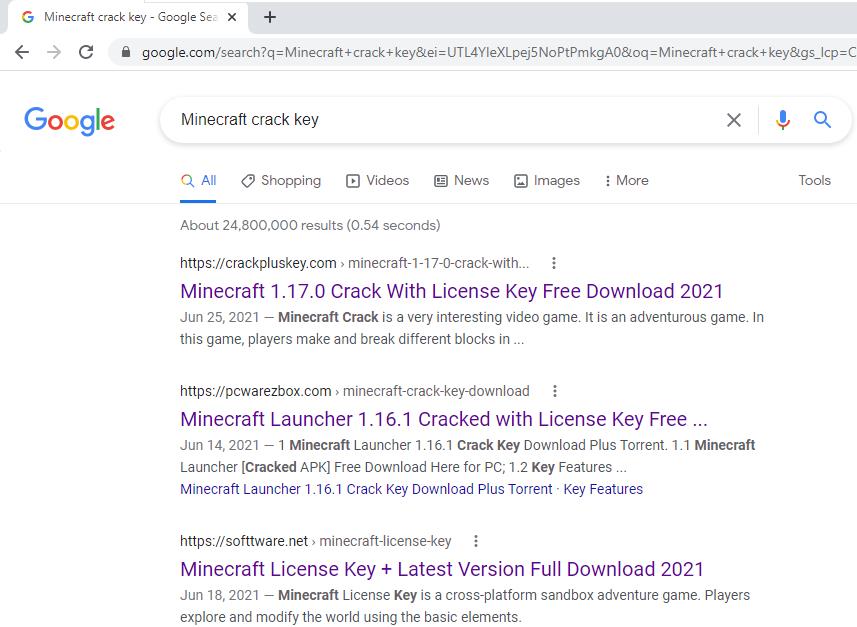
The dropper was introduced through various sites that imitate platforms for illegal free software distribution. Many such sites distribute malware under the guise of keys for programs, including antivirus software, photo and video editors, as well as popular games.

An example of a site page with hacked software for distributing סוורז.
The attackers used the following games as bait: Among US, Battlefield 4, Battlefield V, Control, Counter-Strike Global Offensive, FIFA 21, Fortnite, Grand Theft Auto V, מיינקראפט, NBA 2K21, Need for Speed Heat, PLAYERUNKNOWN’S BATTLEGROUNDS, Rust, The Sims 4, Titanfall 2. Multiple tags were used for each post to make landing pages appear at the top of search results.
The dropper was distributed in a ZIP archive, which contained another password-protected ZIP file and a text file containing this password. The launch of the malware resulted in the decryption and activation of the Taurus stealer Trojan.
לפיכך, at the first stage of infection, the Swarez dropper executes an obfuscated CMD script that decrypts the legitimate AutoIt interpreter. Using it, the malware executes the AutoIt script, which is also obfuscated. Several checks are made to ensure that the file is not being executed in an emulated environment, and then the payload is decrypted using the RC4 algorithm. The resulting file is embedded in one of the system processes and executed in its context. This is Taurus, a paid stealer Trojan developed by the Predator קבוצת פריצה, with many features and customization options. It can steal cookies, saved passwords and autofill data from browsers, secrets for accessing cryptocurrency wallets, collect system information, text files from the user’s desktop, and even take screenshots. The Trojan sends all this information to the C&שרת C.
Let me remind you that I also recently wrote that TrickBot קיבל מודול חדש לניטור קורבנות.




