Prynt Stealer-Malware wird im Dark Web für nur verkauft $100 pro Monat
Cybersecurity specialists from Cyble entdeckt haben a new information-stealing malware called Prynt Stealer. The malware has a wide range of capabilities and comes with additional keylogger and clipper modules.
Prynt-Stealer is advertised as a solution to compromise a wide variety of browsers, instant messengers and gaming applications, and it is also capable of carrying out direct financial attacks.
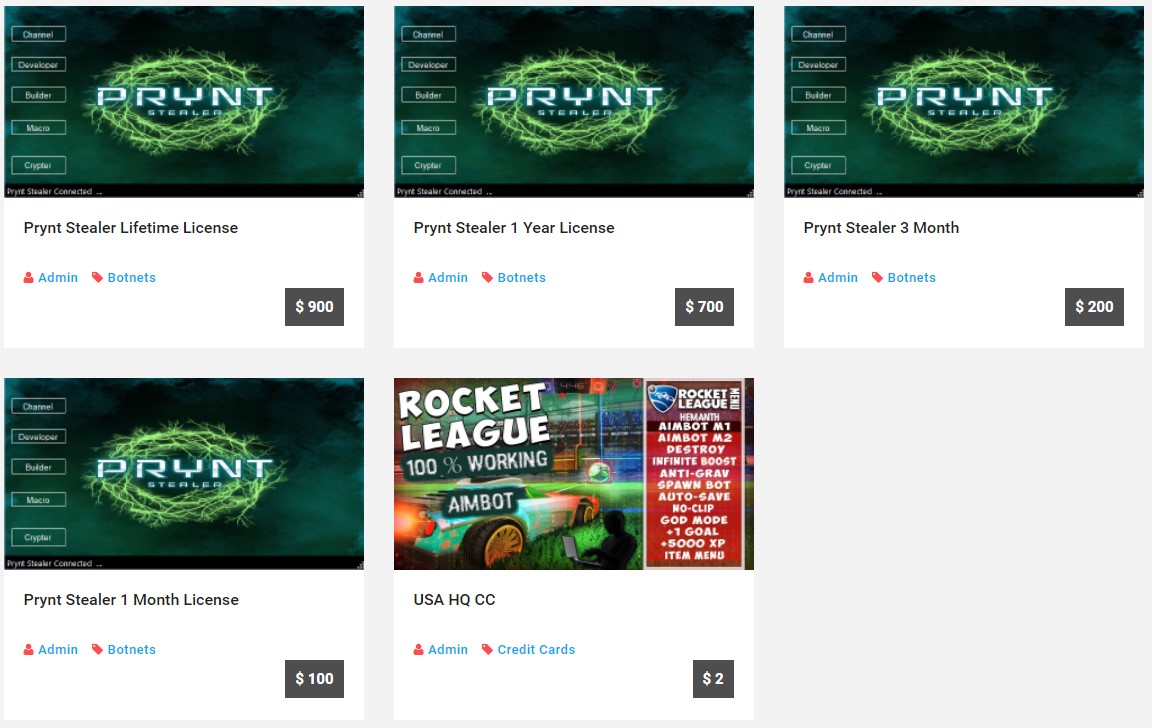
Prynt Stealer is a subscription service and the authors charge $100/month, $200/quarter, or $700/year, and offer a lifetime license for $900.
Apropos, if you are interested in the darknet criminal life, you might like our article: Darknet sites of the REvil group are working again: haben die Russen Cyberkriminelle in die Wildnis entlassen? or you might be interested in this information: RedLine-Dieb malware is the main source of credentials in two major marketplaces.
Außerdem, buyers can use the constructor to create their own, compact and hard-to-detect version of the malware that can be used in targeted attacks.
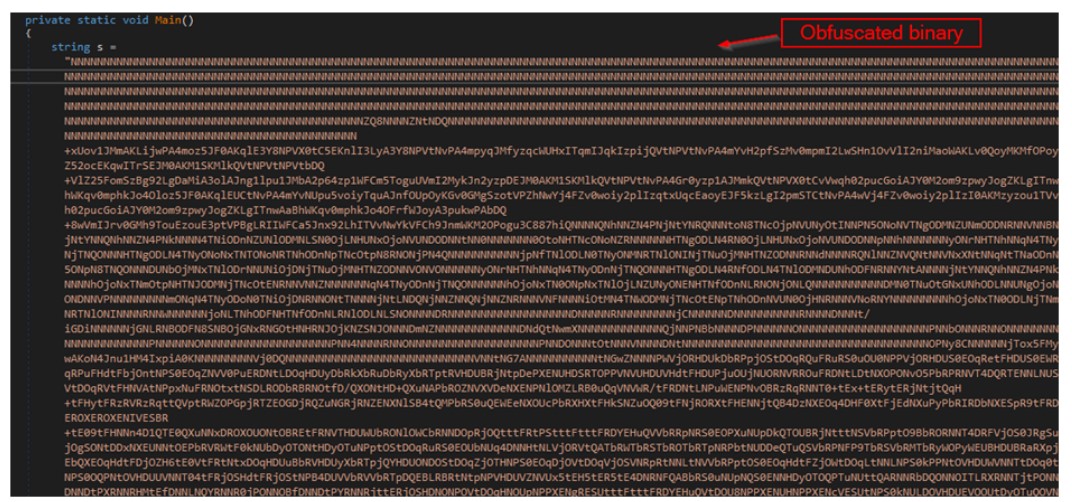
Cyble analysts write that Prynt Stealer was created with an emphasis on stealth and uses binary obfuscation and string encryption using Rijndael. In Ergänzung, all communications with the management servers are encrypted using AES256, and the AppData folder (and subfolders) needed to temporarily store stolen data is hidden.
Once on the victim’s machine, Prynt Stealer scans all disks on the host and steals documents, database files, source code, and image files smaller than 5120 bytes (5 KB).
Nachdem, the malware switches to browsers based on Chrome, Firefox and MS Edge, stealing autofill data, credentials, bank card information, search history and cookies. At this stage, the malware uses ScanData() to search browser data for keywords related to banks, cryptocurrencies, and porn sites, and steals what it finds if information is found.
After Prynt Stealer attacks messengers, einschließlich Zwietracht, Pidgin und Telegramm, and steals Discord tokens if they are in the system. Game application authorization files, game save files and other valuable data from Ubisoft Uplay, Dampf und Minecraft are also stolen.
Schlussendlich, the malware queries the registry to find the data of cryptocurrency wallets such as Zcash, Armory, Bytecoin, Jaxx, Äther, AtomicWallet, Guarda und Coinomi, and also steals information from FileZilla, OpenVPN, NordVPN and ProtonVPN by copying the corresponding credentials to the one mentioned above. subfolder in AppData.
The data transfer itself is carried out using a Telegram bot, which uses an encrypted network connection to upload the dump to a remote server.
Wie oben erwähnt, in addition to these functions, the malware is equipped with keylogger modules (to intercept keystrokes) and a clipper (tracks and replaces cryptocurrency addresses in the clipboard).




