Microsoft предупреждава за повишена активност на злонамерен софтуер XorDdos
Експертите на Microsoft предупредиха, че активността на XorDdos, модулен зловреден софтуер, използван за хакване на Linux устройства и създаване на DDoS ботнет, се е увеличил с 254% през последните шест месеца.
Този зловреден софтуер, известен също като XOR.DDoS и XOR DDoS, е активен оттогава 2014 и е насочен към Linux системи. Той получи името си поради използването на XOR-базирано криптиране, който се използва при обмен на данни с управляващи сървъри, както и поради DDoS атаките, които се извършват с негова помощ.
Напомням, че и ние съобщихме за това Външният вид на Евтини DarkCrystal RAT Malware Притеснени експерти.
XorDdos обикновено се разпространява чрез сканиране на отворени SSH и Telnet портове и последващи груби атаки. За да се разпространи на повече устройства, зловреден софтуер използва shell скрипт, който се опитва да влезе като root, изпробване на различни пароли за хиляди системи, налични в интернет
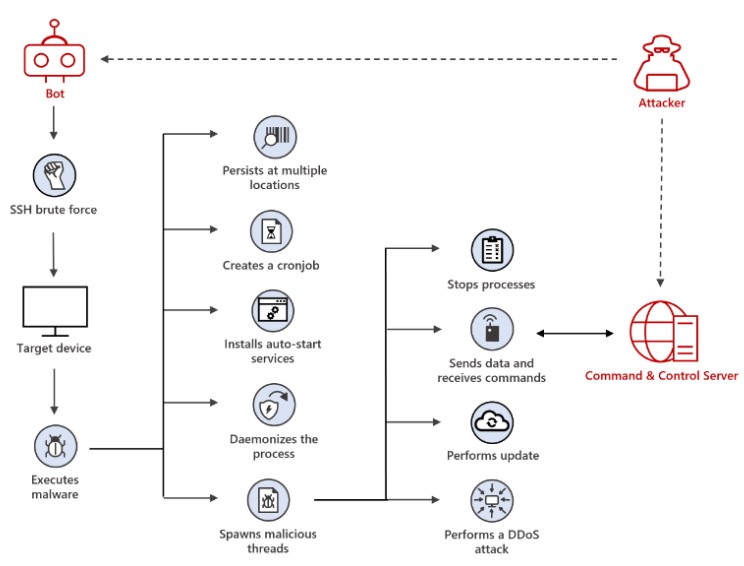
Схема за атака на XorDdos
Според специалисти, успехът на този ботнет се обяснява главно с използването на различни тактики за избягване и методи за поддържане на стабилно присъствие, което позволява на XorDdos да остане невидим и труден за премахване.
Докладът също така отбелязва, че в допълнение към стартирането на DDoS атаки, операторите използват XorDDoS за инсталиране на руткитове, поддържане на достъп до хакнати устройства, и е вероятно да достави допълнителен полезен товар.




