XLoader Botnet Operators Mask C&C Servers Using Probability Theory
Check Point has discovered a new version of the XLoader botnet, an information-stealing botnet that attacks Windows and MacOS systems that uses a new way to mask C&C servers.
According to experts from Check Point, the new version of XLoader uses probability theory to “hide” attackers’ C&C servers, making malware very difficult to detect.
High stealth is achieved by hiding the domain name of the real C&C server along with a configuration containing 64 fake domains, from which 16 domains are randomly selected, and then two of these 16 are replaced with a fake C&C address and a real address.
You might also be interested to know what Russian Fronton Botnet Can Do Much More than Massive DDoS Attacks.
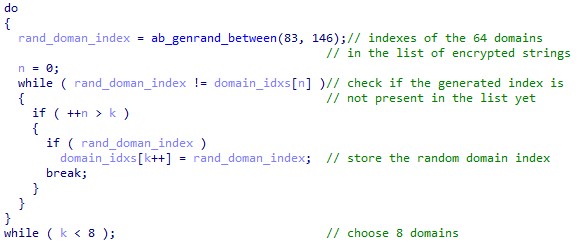
In new versions of XLoader, the mechanism has changed: after selecting 16 false domains from the configuration, the first eight domains are overwritten and given new random values before each communication cycle. At the same time, measures are taken to skip the real domain.
In addition, XLoader 2.5 replaces three domains from the created list with two fake server addresses and the real C&C server domain. The ultimate goal of the hackers is obvious – to prevent the discovery of the real C&C server, based on the delays between accesses to the domains.
XLoader first creates a list of 16 domains that are randomly selected from the 64 domains stored in the configuration. After each attempt to access the selected 16 domains, the following code is executed: