New JavaScript malware RATDispenser used to distribute RAT
Security experts at HP have discovered a new JavaScript malware called RATDispenser. The malware is used as a dropper: to infect systems and then deploy Remote Access Trojans (RAT).
According to experts, RATDispenser has been spreading for more than three months through spam emails with malicious attachments.
These files use the classic double-extension trick (filename.txt.js): they pretend to be text files, but when opened, they run JavaScript code.
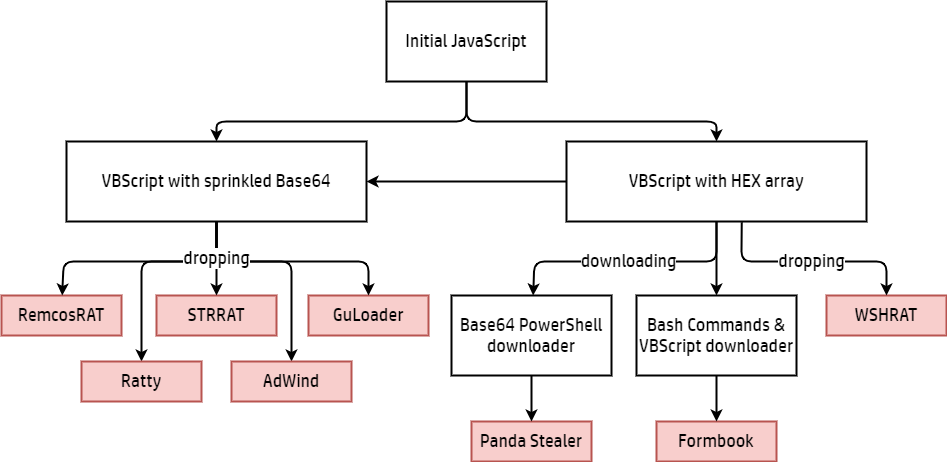
If the user launches such a file, the RATDispenser malware decodes itself and launches a stand-alone VBScript, which then installs a remote access Trojan on the infected device. Over the past three months, malware has been used to spread at least eight different RATs, including STTRAT, WSHRAT, AdWind, Formbook, Remcos, Panda Stealer, GuLoader and Ratty.
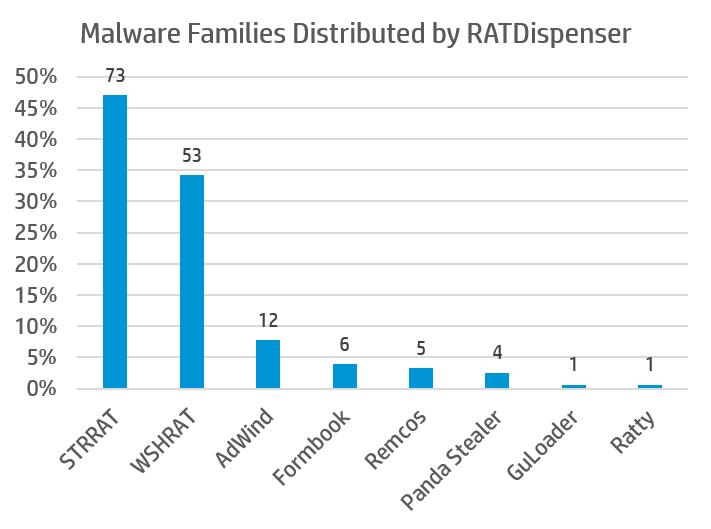
The most interesting among them is Panda Stealer. This new family of malware, first seen in April 2021, targets cryptocurrency wallets. All of the Panda Stealer samples analyzed by the Hewlett Packard researchers were fileless variants that download additional payload from the paste.ee text storage site.
Let me remind you that we also talked about the fact that New BotenaGo Botnet Uses 33 Exploits against IoT Devices.




