Password Thief RedLine Stealer Continues Its Triumphant March around the Planet
Bitdefender information security company specialist spoke about the campaign discovered at the beginning of this year to distribute the RedLine Stealer password thief.
This month alone, cybercriminals carried out 10,000 attacks in more than 150 countries and regions around the world, including the United States, Germany, Egypt, China, and Canada. However, the actual number of attacks may be higher, as the experts only took into account the number of notifications from Bitdefender’s security solutions.
By the way, we also talked about this malware in the article: RedLine Stealer malware is the main source of credentials in two major marketplaces.
RedLine Stealer is a password stealing software that can be bought on hacker forums at a very low price. During the campaign detected by Bitdefender, malware is distributed using the RIG Exploit Kit through the CVE-2021-26411 vulnerability in Internet Explorer.
Judging by the number of countries attacked, the infostealer is not geared towards attacks on any particular country.
When executed on the attacked system, RedLine Stealer searches for usernames, as well as information about hardware, installed browsers and antivirus solutions, and extracts data such as passwords, saved bank card data, cryptocurrency wallets, credentials for VPN services, etc.
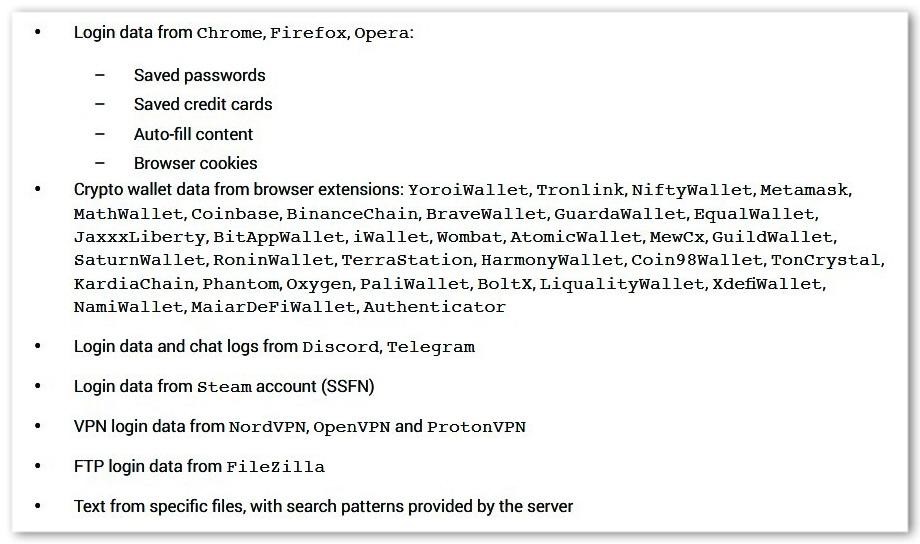
Data stolen by RedLine Stealer
With RedLine Stealer, hackers can extract credentials from browsers, FTP clients, email apps, instant messengers, and VPN services, and sell them on the dark web.




