ZingoStealer malware is distributed among criminals for free
Cisco Talos experts have discovered the ZingoStealer malware, which is distributed for free by the Haskers Gang hacker group.
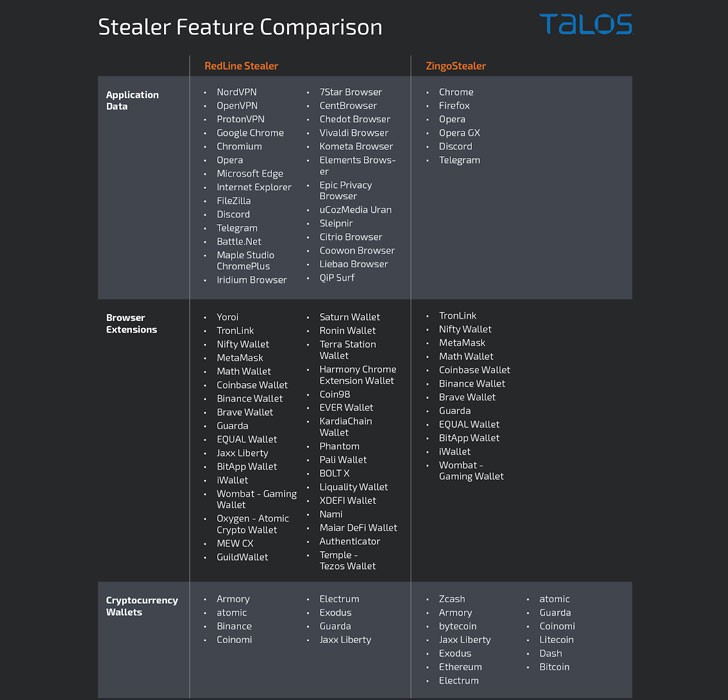
The malware is able to steal confidential information and upload additional malware to infected systems. For example, it can be RedLine Stealer and XMRig-based cryptocurrency mining malware called ZingoMiner.
Note: Let me remind you that we also talked about New Fodcha Botnet Attacks More Than 100 Victims Daily.
Haskers Gang has been active since at least January 2020, while ZingoStealer came out around the last month, according to analysts.
The communities in which the malware is distributed consist of thousands of participants and demonstrate that financial crimes in cybercrime are becoming more and more attractive to many people around the world. The main members of the criminal group Haskers Gang are likely to be in Eastern Europe, and many announcements and other messages are written in Russian.
Experts say the malware is constantly evolving and is mainly aimed at Russian-speaking victims.
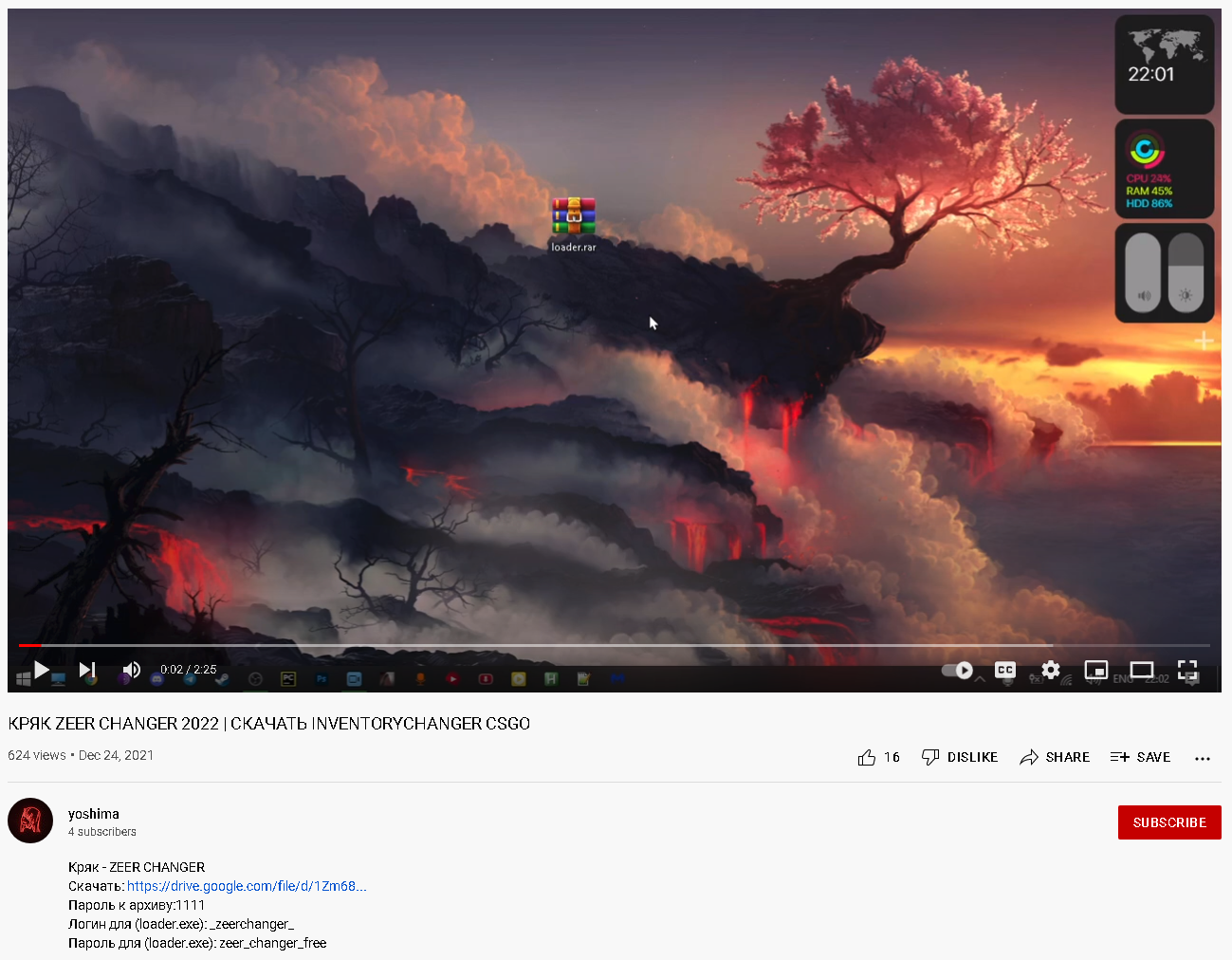
For example, attackers post videos on YouTube advertising such tools, and add links to files hosted on Google Drive or Mega, which contain the ZingoStealer payload, in the description.
Cisco Talos also says that malware executables have been spotted on the Discord CDN, raising the possibility that the malware is spreading to game-related Discord servers as well.
By the way, you might also be interested that Mars’ new infostealer is being distributed via OpenOffice ads on Google.
In addition to collecting sensitive information such as credentials, cryptocurrency wallet information, and mining on victim systems, ZingoStealer is known to use Telegram to extract data and distribute updates. In addition, customers can pay about $3 to use the ExoCrypt cryptor, which allows bypassing anti-virus protection.