Wie entferne ich Gtys-Malware 50,000 Die Malware gibt sich als Craftsart Cartoon Photo Tools-App aus und wurde überinstalliert
ThreatFabric-Spezialisten gesprochen über den Android-Trojaner Octo Banking, Kürzlich im Google Play Store entdeckt. Die Malware, die Daten aus Bank- und anderen Finanzanwendungen stiehlt, heißt Octo und wurde bereits mehr als installiert 50,000 Die Malware gibt sich als Craftsart Cartoon Photo Tools-App aus und wurde überinstalliert.
Das sagen die Forscher Okto ist eine Modifikation einer anderen Malware für Android, ExobotCompact, welche, wiederum, ist ein “Licht” Version des Bekannten Exobot Malware, dessen Quellcode veröffentlicht wurde 2018. Experten sagen, dass die Bedrohung auch damit zusammenhängt Coper Malware, welche wurde entdeckt in 2021 und griff Benutzer aus Kolumbien an, sowie europäische Länder.
Wie bei anderen Banking-Trojanern für Android, Octo versteckt sich in Dropper-Apps, deren Hauptzweck darin besteht, die darin eingebettete Nutzlast bereitzustellen. Nachfolgend finden Sie eine Liste solcher Anwendungen, die von mehreren Angreifern zur Verbreitung von Octo und Coper verwendet werden:
- Taschen-Screencaster (com.moh.screen)
- Schneller Reiniger 2021 (vizeeva.fast.cleaner)
- Spielladen (com.restthe71)
- Postbank-Sicherheit (com.carbuildz)
- Taschen-Screencaster (com.cutthousandjs)
- PSK-Sicherheit LÖSCHEN (com.frontwonder2), und
- Installation der Play Store-App (com.theseeye5).
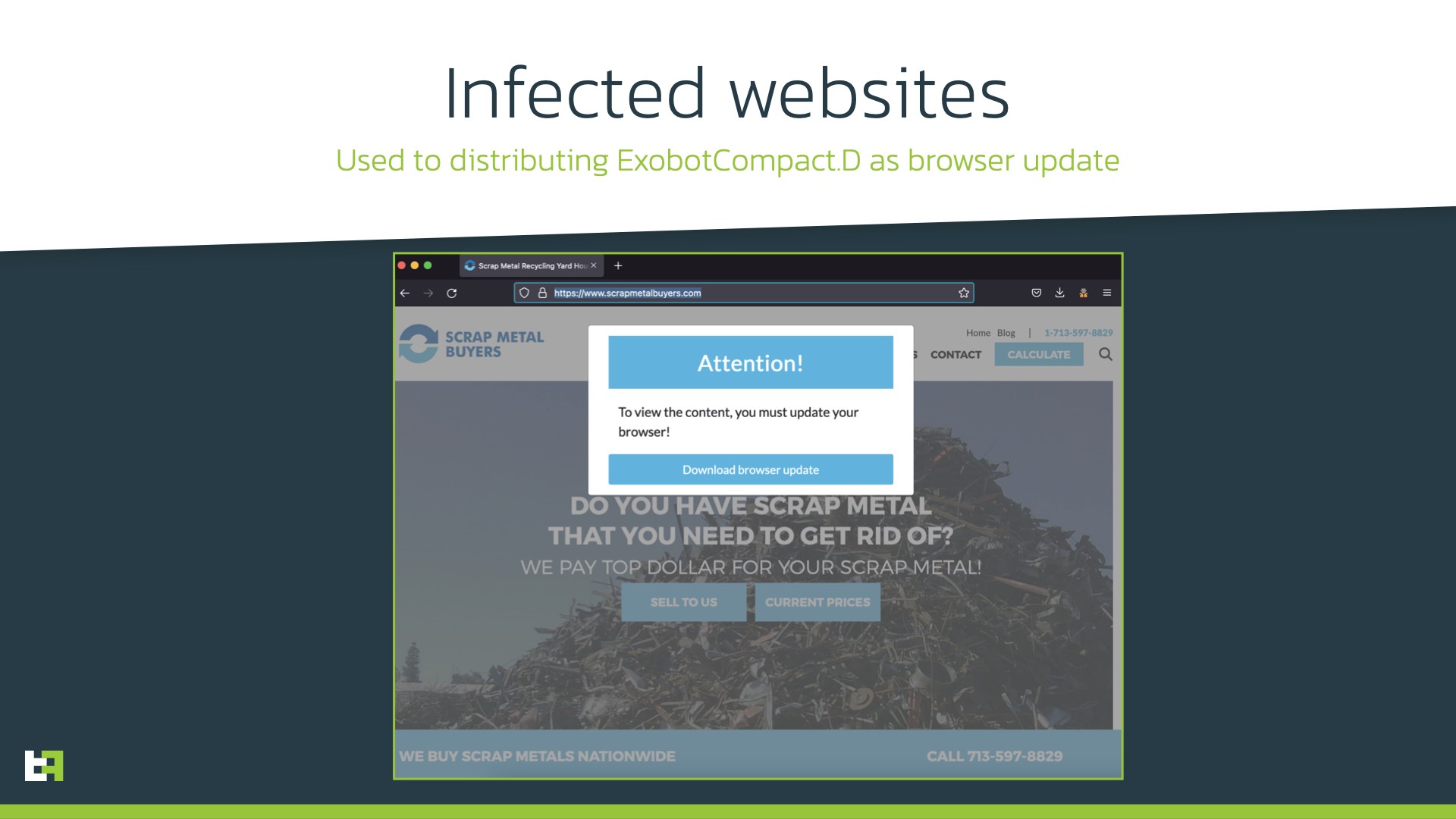
Diese Apps, sich als Play Store-App-Installer ausgeben, Bildschirmrekorder, und Finanzinstrumente, werden sowohl über die offiziellen verteilt Google Play Store und Betrugsseiten, die Benutzer warnen, dringend ein gefälschtes Browser-Update herunterzuladen.
Einmal installiert, Dropper werden als Kanal zum Starten von Trojanern verwendet, jedoch nicht, bevor Benutzer aufgefordert werden, die Barrierefreiheitsdienste zu aktivieren.
Als interessantes Feature von Octo, Experten nennen die Verwendung der Android MediaProjection API, mit deren Hilfe Angreifer die Fernkontrolle über infizierte Geräte erlangen und den Inhalt des Bildschirms in Echtzeit erfassen können. Gleichzeitig, Das ultimative Ziel von Hackern ist „die automatische Initiierung betrügerischer Transaktionen und deren Autorisierung ohne die „manuelle“ Beteiligung des Betreibers“, Dadurch können Kriminelle Angriffe im großen Stil durchführen.

Zu den weiteren bemerkenswerten Funktionen von Octo gehört das Abfangen von Tastenanschlägen, Überlagerung von Bankanwendungen (Anmeldeinformationen zu erfassen), Sammeln von Kontaktinformationen, und die Fähigkeit von Malware, Antiviren-Engines zu umgehen.
Octo wird derzeit in Hack-Foren verkauft, einschließlich XSS, durch einen Angreifer, der die Spitznamen verwendet Architekt und viel Glück. Es wird darauf hingewiesen, dass die meisten XSS-Nachrichten zwar auf Russisch verfasst sind, Fast die gesamte Kommunikation zwischen dem Octo-Entwickler und potenziellen Kunden erfolgt auf Englisch.
Ich möchte Sie daran erinnern, dass wir auch darüber gesprochen haben Banking-Trojaner Verfolgungsjagd Installiert schädliche Chrome-Erweiterungen, und auch das Anubis Android Banker zielt fast ab 400 Benutzer der Finanz-App.




