Ang Linux malware FontOnLake gigamit sa mga gipunting nga pag-atake
ESET specialists talked about the FontOnLake malware, nga naghiusa sa mga sangkap sa backdoor ug rootkit. The malware is known to be used in targeted attacks against organizations in Southeast Asia.
Experts write that the first file related to this malware family appeared on VirusTotal back in May last year, and other samples were uploaded during the year. Based on where these files were downloaded from, the researchers concluded that FontOnLake was primarily used in Southeast Asia. At the time of this writing, all the malware’s control servers had already been disabled. But the researchers note that, as a rule, during targeted attacks, hackers act in this way: the work of the infrastructure stops as soon as their goals are achieved.
It is known that FontOnLake is distributed through trojanized applications, but researchers do not know how the attackers forced their victims to download modified binaries. Among the utilities that the attacker modified to deliver FontOnLake were cat, kill, sftp, and shd.
According to the researchers, the trojanized utilities were probably modified at the source code level, mao, the attackers compiled them and replaced the original.
Usab, the modified binaries provided loading of additional payloads, collecting information and performing other malicious actions. The fact is that FontOnLake has several modules that interact with each other and allow hackers to steal confidential data, effectively hiding their presence in the system.
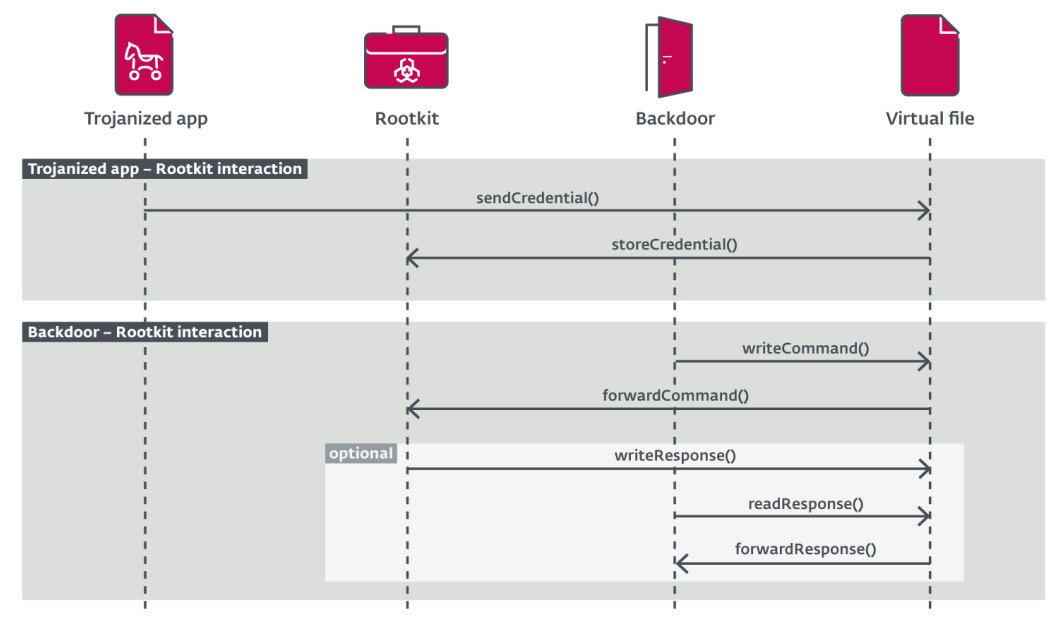
The experts also discovered three custom backdoors written in C ++ and related to FontOnLake. They provide malware operators with remote access to the infected system. A common feature for all backdoors is to pass the collected sshd credentials and bash command history to the command and control server.
The presence of FontOnLake in a compromised system is also masked by a rootkit, which is also responsible for updating and delivering backup backdoors. All rootkit samples studied by ESET targeted kernel versions 2.6.32-696.el6.x86_64 and 3.10.0-229.el7.X86_64.
Tugoti ko nga pahinumdoman ka nga kami usab ang nagsulat niana Hackers create Cobalt Strike Beacon for Linux.




