BluStealer malware steals cryptocurrency and spreads through phishing emails
Avast analysts talked about a malicious spam campaign spreading BluStealer malware that steals cryptocurrency.
This info-stealer is designed to “pull” Bitcoin, Ethereum, Monero and Litecoin) from popular wallets – ArmoryDB, Bytecoin, Jaxx Liberty, Exodus, Electrum, Atomic, Guarda and Coinomi.
In total, experts tracked more than 12,000 phishing emails around the world.
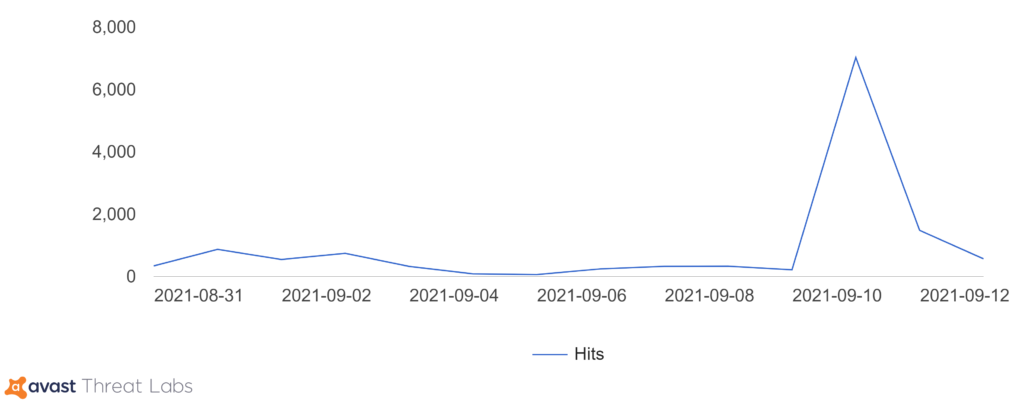
In mid-September, the Avast Threat Intelligence team recorded a surge in malicious activity – phishing emails using the names of the shipping company DHL and the Mexican metallurgical company General de Perfiles, and distributing the BluStealer malware.
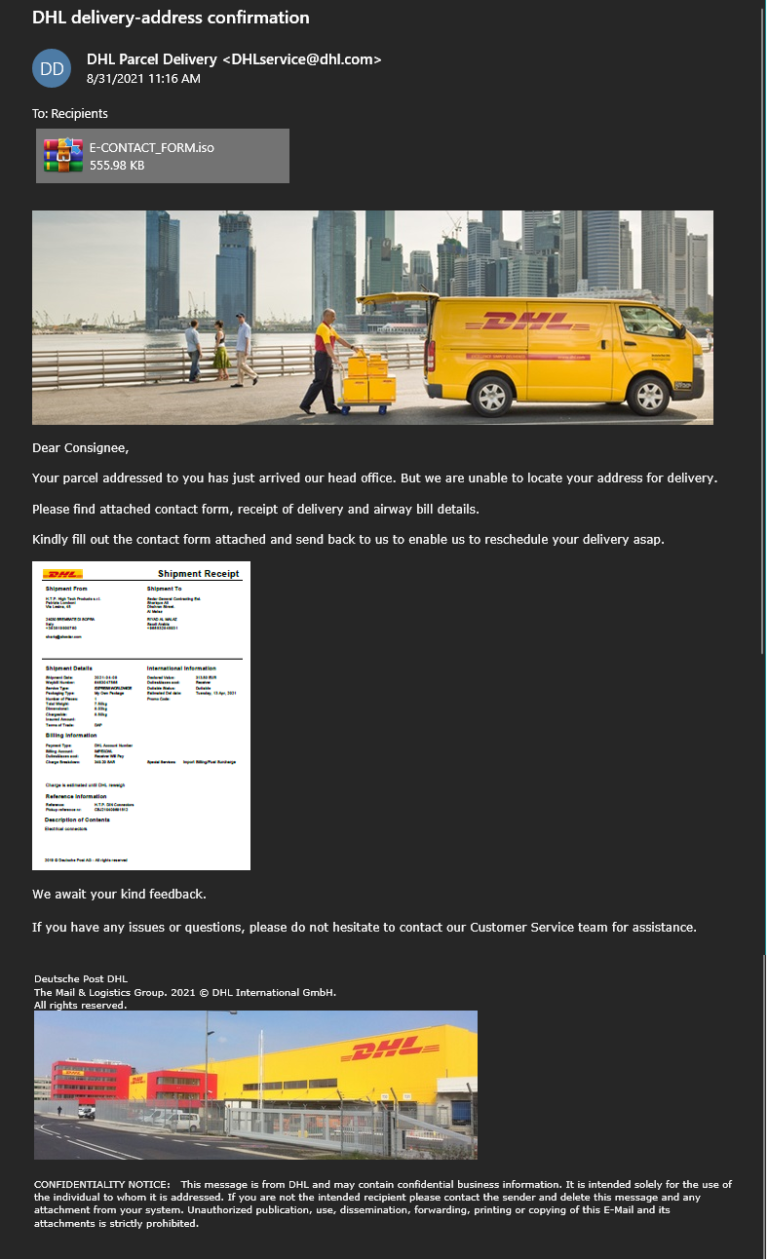
An example of a phishing email
As a rule, in such messages it is said that a certain parcel was delivered to the head office of the company due to the absence of the recipient on the spot. Next, the recipient is asked to fill out the attached document in order to transfer the delivery. When the user tries to open it, the BluStealer installation starts.
In phishing campaigns associated with General de Perfiles, recipients receive emails stating that they have overpaid their bills and that some credit has been saved for them, which will be included in the invoice of the next purchase. As in the campaign imitating DHL, the General de Perfiles message contains BluStealer as an attachment.
The countries most affected by BluStealer are Russia, Turkey, USA, Argentina, UK, Italy, Greece, Spain, France, Japan, India, Czech Republic, Brazil and Romania. So, Russian users received 139 such letters.
A large number of malware samples studied by Avast belonged to one specific campaign, which was identified by the unique .NET downloader. For example, spam messages contained .iso attachments and download URLs. These attachments contain executable malware files packaged using the mentioned .NET loader.
Let me remind you that I also told that BulletProofLink Cybercrime Offers Phishing as a Service.




