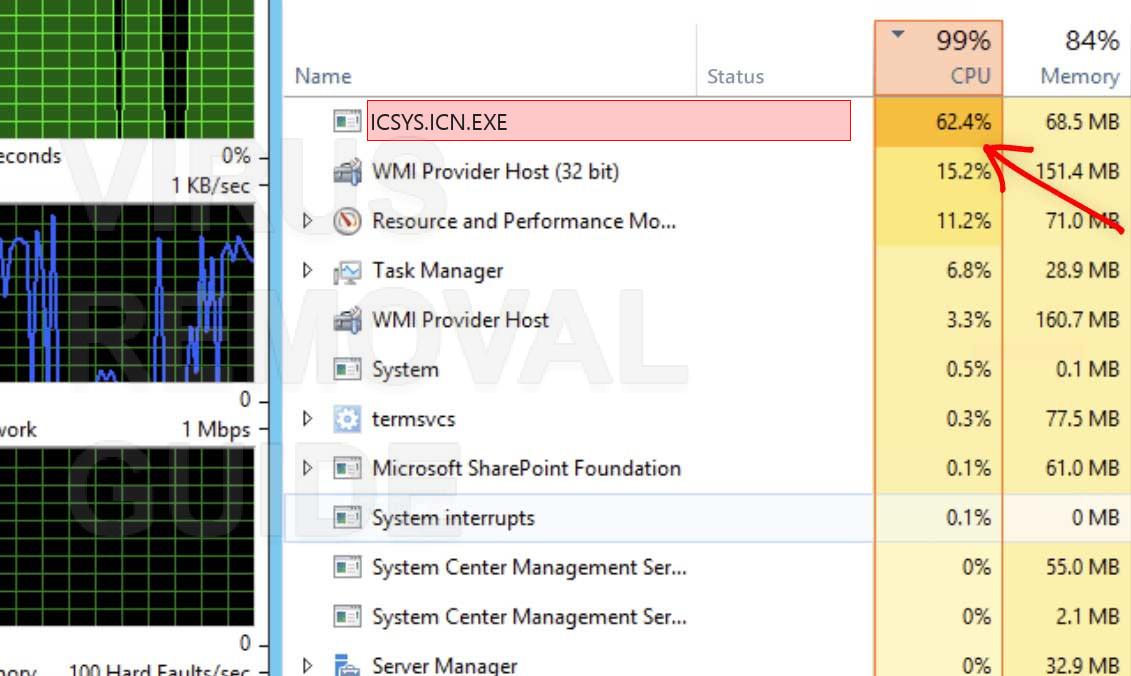
- 惡意進程

[解決] 特洛伊木马Connectd.exe捲土重來
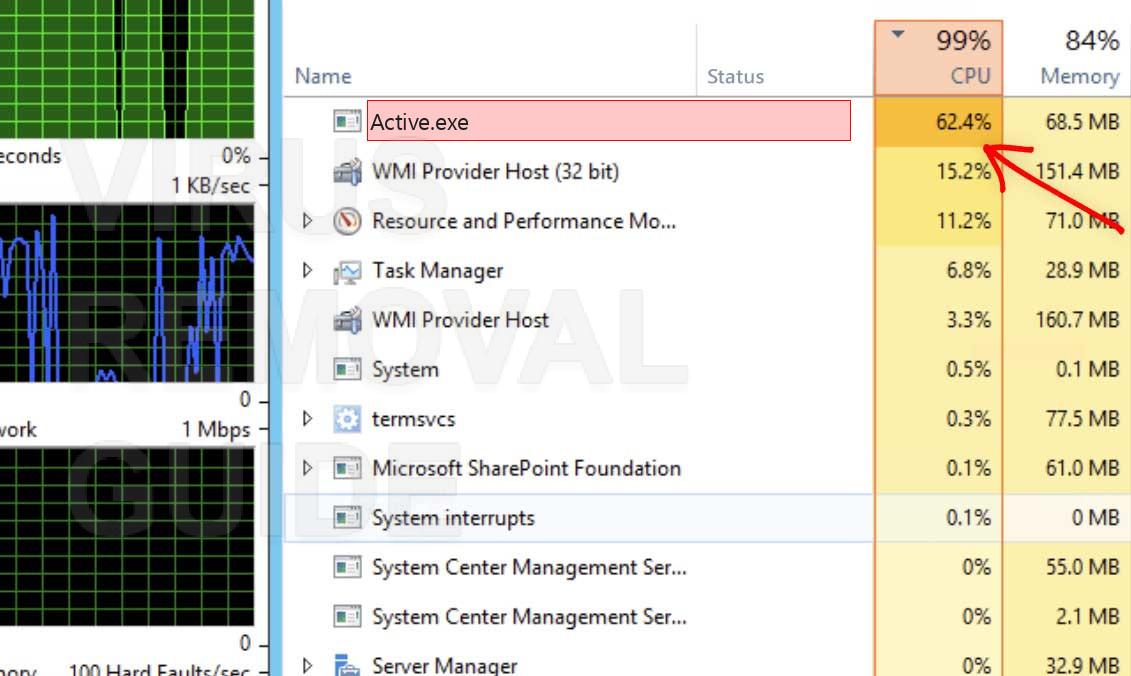
關於 Connectd.exe Connectd.exe 係一種木馬,佢會濫用你嘅 CPU 嘅力量去挖掘電子貨幣,而呢種貨幣嘅名稱係 Monero. 佢係下載同安裝到啲隱藏嘅資料夾入面同埋…
閱讀更多 » -
-
-
-
-
-
-
-
- 三月- 2018 -6 三月惡意進程
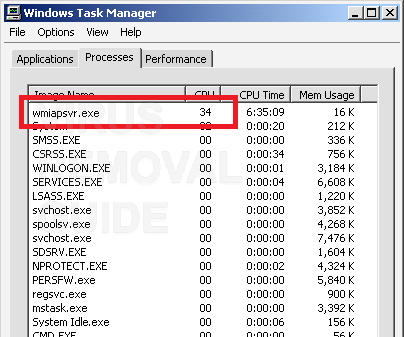
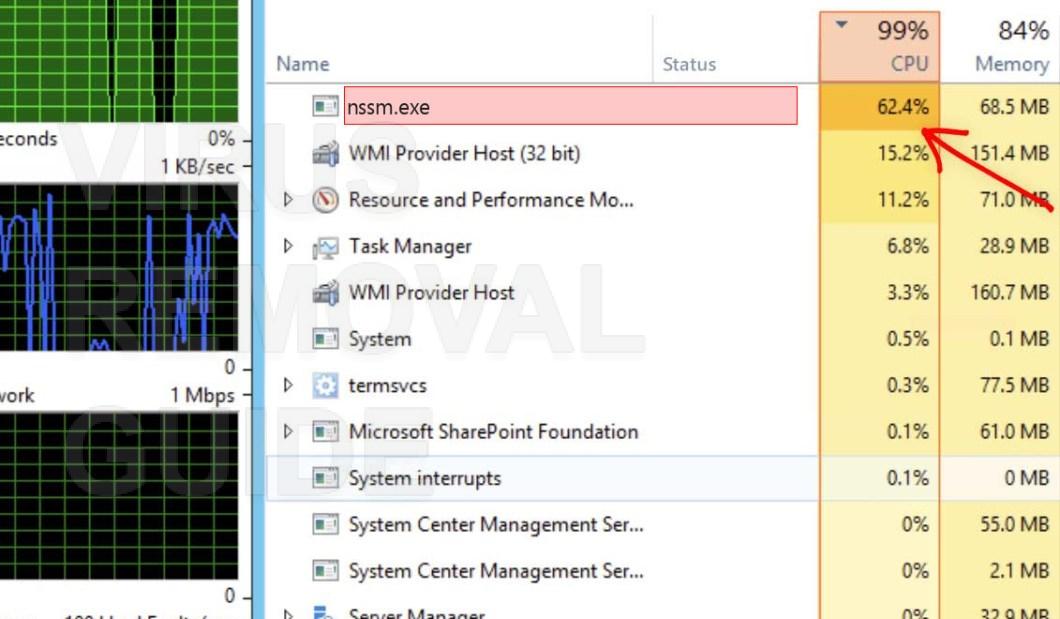
wmiapsvr.exe trojan miner. How to kill wmiapsvr.exe process?
wmiapsvr.exe is a consequent part of a malicious Trojan Horse. You may hear about it…
閱讀更多 » - 3 三月惡意進程
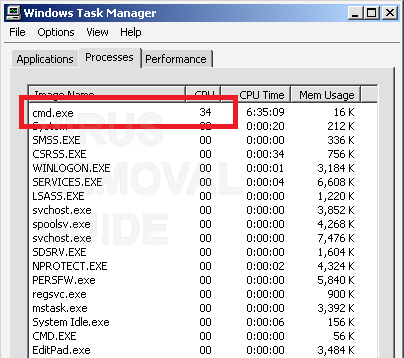
cmd.exe trojan miner. How to kill cmd.exe process?
cmd.exe makes a part of a Trojan Horse. The main aim of this process is…
閱讀更多 » - 3 三月惡意進程
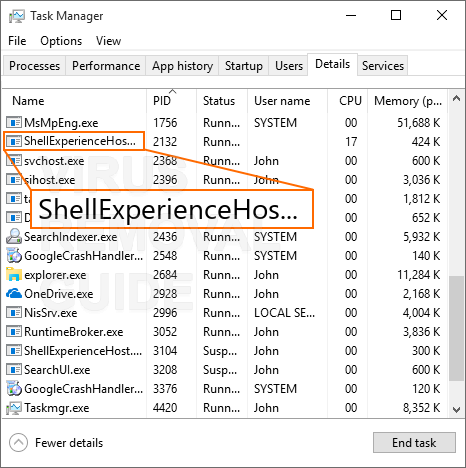
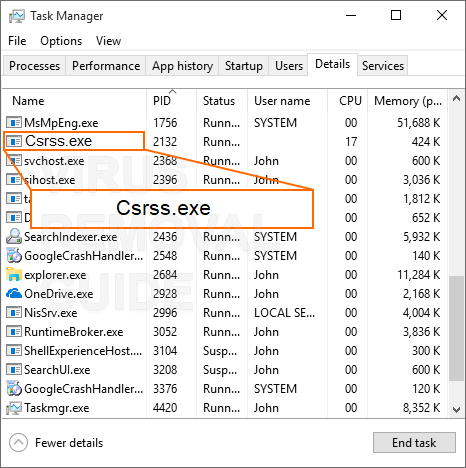
ShellExperienceHost.exe overloads CPU. How to get rid of ShellExperienceHost.exe trojan?
ShellExperienceHost.exe is malicious software that is used with fraudulent purposes by hijacking virus software in…
閱讀更多 » - 二月- 2018 -26 二月惡意進程
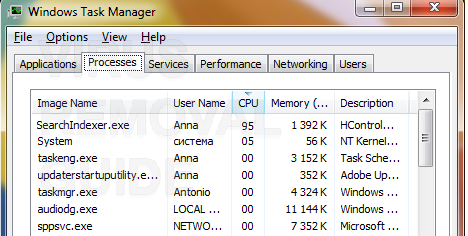
SearchIndexer.exe slowly kills CPU. SearchIndexer.exe remedy
The SearchIndexer.exe operation relates to a Trojan Horse penetration. It violates popular digital currency making…
閱讀更多 » - 26 二月惡意進程
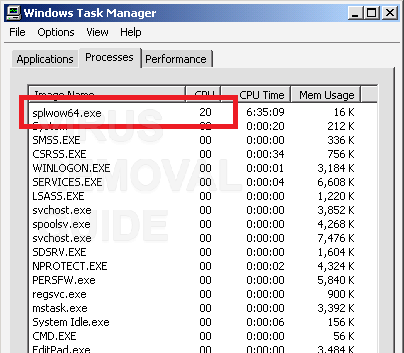
splwow64.exe overloads CPU. How to get rid of splwow64.exe trojan?
splwow64.exe is a horror story for digital coins. Owners of Bitcoins, 門羅幣, and different others…
閱讀更多 » - 23 二月惡意進程
OSE.EXE overloads CPU. How to get rid of OSE.EXE trojan?
OSE.EXE makes a part of a Trojan Horse. The main aim of this process is…
閱讀更多 » - 19 二月惡意進程
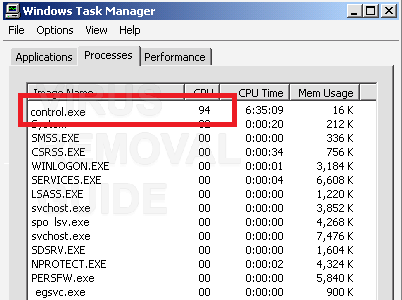
CPU is exhausted by control.exe. How to deal with control.exe trojan coin miner?
control.exe is malicious software that is used with fraudulent purposes by hijacking virus software in…
閱讀更多 » - 19 二月木馬

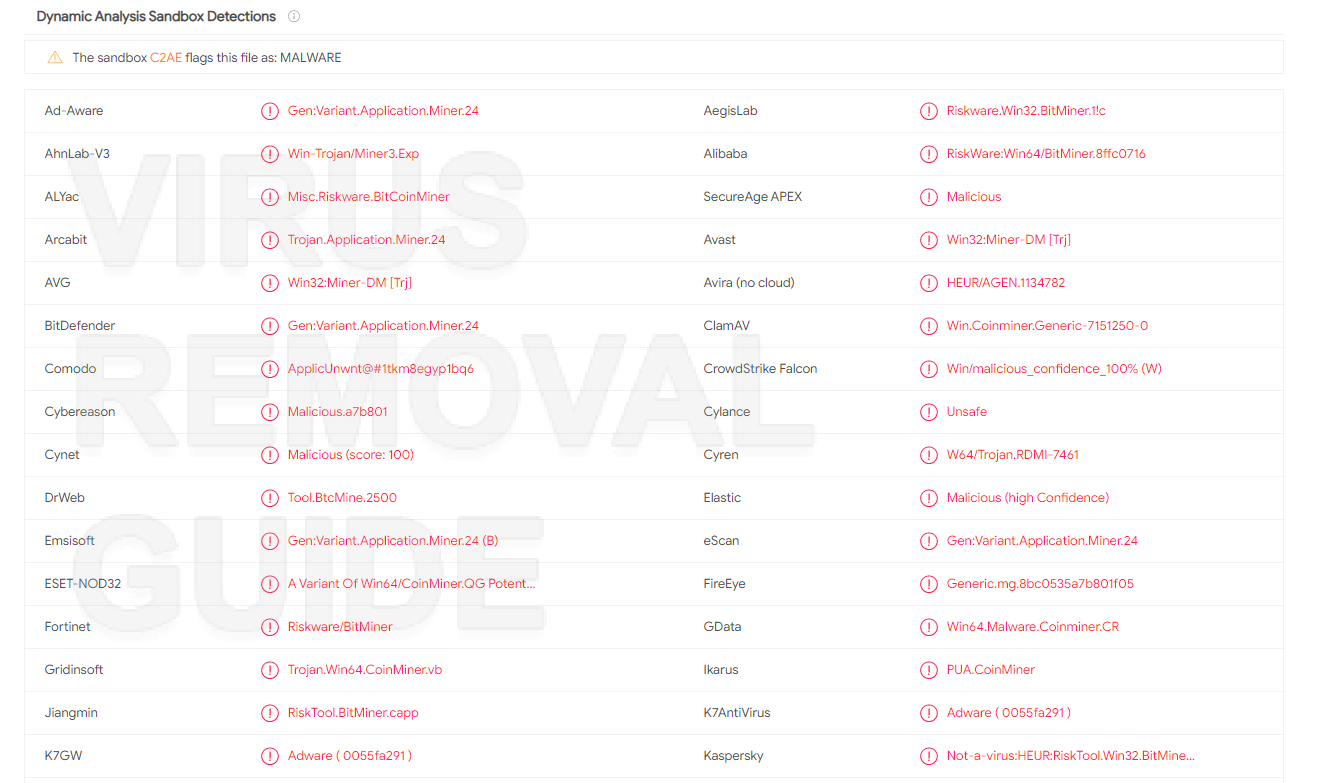
Win32.HackTool.CoinMiner Coin Miner Detection and Deleting
Win32.HackTool.CoinMiner infects the targeted computer with the aim to use its resources for disrupting digital…
閱讀更多 » - 16 二月惡意進程
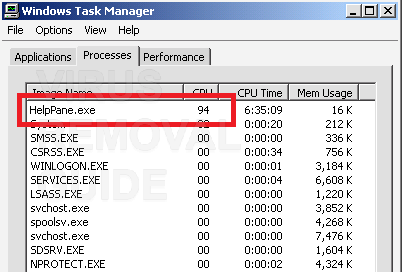
Extraordinarily rapid CPU usage from HelpPane.exe? How to eliminate HelpPane.exe trojan coin miner?
HelpPane.exe is an essential part of a Trojan Horse. You may know it as a…
閱讀更多 » - 12 二月惡意進程
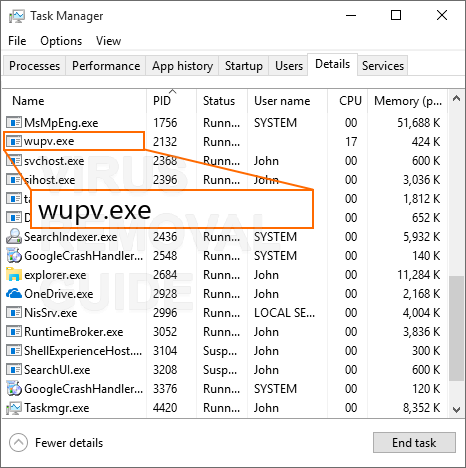
CPU因wupv.exe耗盡. 如何處理wupv.exe木馬幣挖礦程序?
wupv.exe is malicious software that is used with fraudulent purposes by hijacking virus software in…
閱讀更多 »